To use Anti-Malware, perform these basic steps:
Procedure
Next steps
When you have completed these steps, review Configure malware scans and refine the Anti-Malware scan behavior.
For most Anti-Malware settings, you can either configure them for each individual
computer or in a policy that applies to multiple computers (for example, to all Windows
2008 Servers). To make management easier, configure the settings in the policy (not
individual computers) wherever possible. For more information, see Policies, inheritance, and overrides.
CPU usage and RAM usage varies by your Anti-Malware configuration. To optimize Anti-Malware
performance on the agent, see Performance tips for Anti-Malware.
For an overview of the Anti-Malware feature, see Protect against malware.
Enable the Anti-Malware module
Procedure
- Go to Policies.
- Double-click the policy for which you want to enable Anti-Malware.
- Go to .
- From Anti-Malware State, select On.
- Click Save.
Select types of scans to perform
When Anti-Malware is turned on, Server & Workload Protection needs to know what type of scans it should perform (see Types of malware scans).
Procedure
- Go to Policies.
- Double-click the policy to configure.
- Click .
- Enable or disable each type of scan:
- To perform the scan using default settings, select Default.
- To perform the scan using a malware scan configuration that you can customize, select a malware scan configuration.
- To disable the scan, for the malware scan configuration select No Configuration.
- Click Save.
Next steps
TrendAI™ recommends that you configure Server & Workload Protection to perform weekly scheduled scans on all protected servers. You can do this using
Scheduled Tasks. See Schedule Server & Workload Protection to perform tasks.)
Configure scan inclusions
To reduce scanning time and minimize the use of computing resources, you can configure
malware scans to include only specific folders, files, and file types in all types
of scans. You can also include process image files in real-time malware scans that
are run on Windows computers. For more information, see Configure malware scan inclusions.
All inclusions are specified by selecting inclusion lists on the Inclusions tab of the Malware Scan Configuration editor. Lists can be either inherited or non-inherited.
You can select multiple lists for your inclusions list.
ImportantTo allow configuring of multiple inclusion lists, you must first select an inclusion
list in the malware scan configuration inclusions. Selecting all directories or all
files disables adding lists for the inclusion type. For more information, see Configure malware scan inclusions.
|
Procedure
- Go to Policies.
- Double-click the policy you want to configure.
- Go to .
- Select the type of scan type to configure inclusions.
- Real-time
- Scheduled
- Manual
- To add all inherited lists, select Use inherited lists.
- To add non-inherited lists, select a list from the drop-down and click Add.
- To create a new list, select New...For details, see Create a list of files for use in policies.
- To edit an added list, click the edit icon (
 ).
). - To remove a list, click the delete icon (
 ).
). - Click Save.
Configure scan exclusions
-
To allow configuring of multiple exclusion lists, you must first select an exclusion list in the malware scan configuration exclusions. Clearing or disabling an exclusion list disables adding lists for the exclusion type. For more information, see Configure malware scan exclusions.
-
Recommended Exclusions is not available in all regions.
-
Recommended Exclusions supports TrendAI Vision One™ Endpoint Security agent version 202501 and later (Server & Workload Protection version 20.0.2.1390 and later). Activity Monitoring must be enabled for agent version 202503 and earlier (Server & Workload Protection version 20.0.2.4960 and earlier).
-
Recommended Exclusions requires firewall settings to allow Internet of Things (IoT) traffic to Amazon Web Services.
-
Automatically assigning recommended exclusions is an Advanced Server & Workload Protection feature that requires additional credits per endpoint the policy is applied to.
-
Carefully review the recommended exclusions before enabling the feature to ensure any potential security risks are understood for your environment.
To reduce scanning time and minimize the use of computing resources, you can configure
malware scans to exclude specific folders, files, and file types from all types of
scans. You can also exclude process image files from real-time malware scans that
are run on Windows computers. For more information, see Configure malware scan exclusions.
TipIf any performance-related issues are experienced when Server & Workload Protection Anti-Malware protection is enabled, you can use exclusions to help troubleshoot these
issues by excluding specific folders or files from scanning.
|
All exclusions are specified by selecting exclusion lists on the Exclusions tab of the Malware Scan Configuration editor. Lists can be either inherited or non-inherited.
You can select multiple lists for your exclusion list.
Procedure
- Go to Policies.
- Double-click the policy you want to configure.
- Go to .
- To configure exclusions for Real-time scan, click Real-time.
- Configure Recommended Scan settings for Real-time scans.
- To manage whether agents can use recommendation scan results to dynamically apply
exclusions, configure the setting for Automatically assign application-based recommended exclusions.
-
Inherited: Use the parent policy settings.
-
No: Do not automatically assign recommended exclusions.
-
Yes: Automatically assign recommended exclusions.
-
- To manage recommended exclusions manually, click Assign/Unassign in the Assigned Recommended Exclusions list and select the applications you want to exclude from real-time scans.
- To manage whether agents can use recommendation scan results to dynamically apply
exclusions, configure the setting for Automatically assign application-based recommended exclusions.
- To prevent Recommended Exclusions from assigning an application as an exclusion, configure
the application properties.
- Click Assign/Unassign in the Assigned Recommended Exclusions list.
- Click the application you want to exclude and click Properties...
- Go to Options.
- Configure the setting Exclude from Recommendations.
-
Inherited: Use the parent policy settings.
-
No: Recommended Exclusions can assign the application as an exclusion.
-
Yes: Recommended Exclusions cannot assign the application as an exclusion.
-
- Configure the exclusion lists.The following lists can be configured by navigating between Real-Time, Scheduled, and Manual.
-
File List
-
Directory List
-
File Extension List
-
Process Image File List (Real-Time scan only)
-
- To add all inherited lists, select Use inherited lists.
- To add non-inherited lists, select a list and click Add.
- To create a new list, select New...For details, see Create a list of files for use in policies.
- To edit an added list, click the edit icon (
 ).
). - To remove a list, click the delete icon (
 ).
). - Click Save.
Scan for recommended exclusions on computers
-
Recommended Exclusions is not available in all regions.
-
Recommended Exclusions supports TrendAI Vision One™ Endpoint Security agent version 202501 and later (Server & Workload Protection version 20.0.2.1390 and later). Activity Monitoring must be enabled for agent version 202503 and earlier (Server & Workload Protection version 20.0.2.4960 and earlier).
-
Recommended Exclusions requires firewall settings to allow Internet of Things (IoT) traffic to Amazon Web Services.
-
Carefully review the recommended exclusions before excluding any recommendations to ensure any potential security risks are understood for your environment.
To discover if any applications TrendAI™ recommends for Anti-Malware exclusions are installed on your endpoints, you can scan
for recommendations from the Computer editor.
Procedure
- Go to Computers and open the computer editor for the endpoint you want to manage.
- Go to .
- Under Recommended Exclusions, click Scan For Recommendations.The agent scans the endpoint for any installed application on the Recommended Exclusions list. The process might take up to 10 minutes to complete. You can refresh the screen to check for the results. The Last Scan for Recommendations should update once complete.
- After the scan completes, check the number of Detected Applications.If the number is 0, the endpoint does not have any recommended applications not already added to the Assigned Recommeneded Exclusions list.
- To assign more exclusions, click Assign/Unassign.
- Filter the list for Recommended for Assignment.
- Select the applications you want to exclude and click OK.
- Click Save to save the settings.
- To clear the recommendation scan results, click Clear Recommendations.
Ensure that Server & Workload Protection can keep up to date on the latest threats
To remain effective against new viruses and exploits, agents need to be able to download
the latest software and component update packages from TrendAI™ or indirectly, from your own Relay. These packages contain threat definitions and
patterns. Relay-enabled agents, organized into relay groups (also managed and configured
by Server & Workload Protection) retrieve component updates from TrendAI™, and then distribute them to other agents and appliances.
Procedure
- Go to
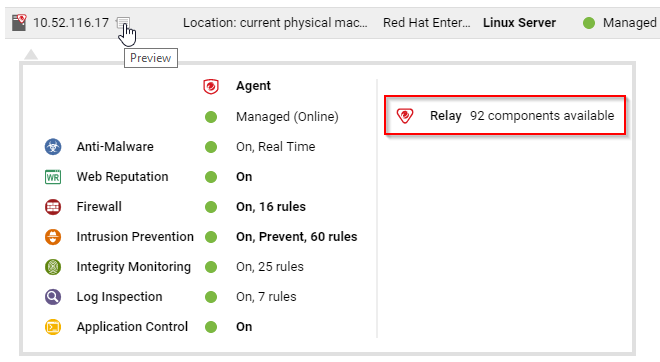
- Configure Server & Workload Protection's ability to retrieve component updates from TrendAI™. Make sure you have at least one relay-enabled agent, and it is assigned to the appropriate
agents and appliances. To determine if an agent is a relay, next to a computer, click
Preview.
- Go to .
- Verify that there is a scheduled task to regularly download available updates for
both component and software updates.


