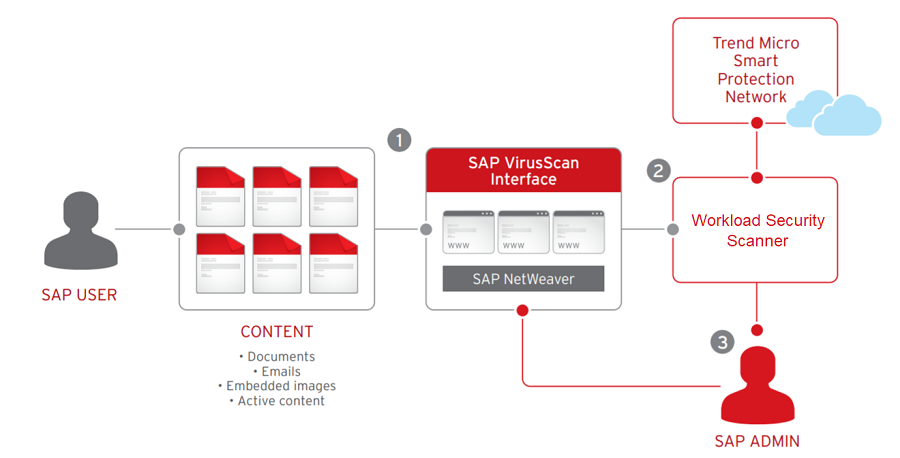
The Scanner feature enables you to protect your SAP deployments using Server & Workload Protection, helping to secure critical information from attack, including a wide variety of
threats such as malware, cross-site scripting and SQL injection. Server & Workload Protection scans content uploaded to the SAP NetWeaver technology platform to determine its
true type and reports this to SAP systems via the NetWeaver-VSI interface. Content
scanning protects against possible malicious script content that might be embedded
or disguised inside documents. SAP administrators can then set policy according to
which document types should be allowed.
Scanner is not supported on computers with a relay-enabled agent.
Architecture
- SAP customer environments are secured through the SAP Virus Scan Interface (VSI), the security component of the SAP NetWeaver platform. The VSI is used to secure all forms of customer content including documents, embedded images, and active content including JavaScript and scripts in PDF and Office documents. The Scanner feature works seamlessly with SAP NetWeaver technology and the SAP HANA® platform.
- The Server & Workload Protection Scanner scans the content uploaded to the SAP NetWeaver technology platform to determine its true type and reports this to SAP systems via the NetWeaver VSI interface. Content scanning protects against possible malicious script content that might be embedded or disguised inside documents.
- SAP administrators can then set policy according to which actual document types should be allowed.
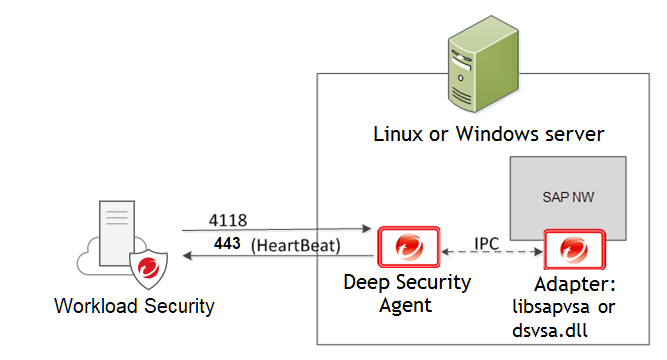
Server & Workload Protection and SAP components
Server & Workload Protection connects with the agent located on the SAP NetWeaver server. The agent connects with
libsapvsa or dsvsa.dll, which are the virus adapters provided by TrendAI™ for scanning purposes.
The following components are involved:
- Server & Workload Protection: The centralized web-based management console that administrators use to configure security policy and deploy protection to the agent.
- Agent: A security agent deployed directly on a computer. The nature of that protection depends on the rules and security settings that each agent receives from Server & Workload Protection.
- SAP NetWeaver: SAP integrated technology computing platform. The SAP NetWeaver Virus Scan Interface (NW-VSI) provides virus scanning capabilities for third-party products that perform the actual scan. The NW-VSI interface must be activated.
- SAP NetWeaver ABAP WinGUI: A Windows management console used for SAP NetWeaver. In this document, it is used for the configuration of the agent and the SAP NetWeaver Virus Scan Interface.
Configure integration of Server & Workload Protection Scanner and SAP NetWeaver
-
See Supported features by platform to obtain information about the operating systems that support Scanner.
-
Install the agent on an SAP application server running one of the supported operating systems. See Install the agent.
-
Add the SAP server to Server & Workload Protection and activate the agent on the SAP server. See Add the SAP server to Server & Workload Protection and activate the agent.
-
Open the computer or policy editor and go to .
-
Enable the SAP integration. See Assign a security profile.
-
Configure the SAP Virus Scan Interface (VSI) by calling the following transactions:
-
VSCANGROUP
-
VSCAN
-
VSCANPROFILE
-
VSCANTEST
-
Depending on your operating system and environment, the output may differ.
Install the agent
The agent is installed with core agent functionality only. After the agent is installed
on SUSE Linux Enterprise Server or Red Hat Enterprise Linux, you can enable protection
modules on the agent. At that point, the plug-ins required for the protection modules
are downloaded and installed.
-
Go to the Deep Security software download page and download the agent package for your OS.
-
Install the agent on the target system. You can use rpm or zypper, depending on the OS. In this example, rpm is used by typing:
rpm -ihv Agent-Core-SuSE_<version>.x86_64.rpm -
Expect the output similar to the following:
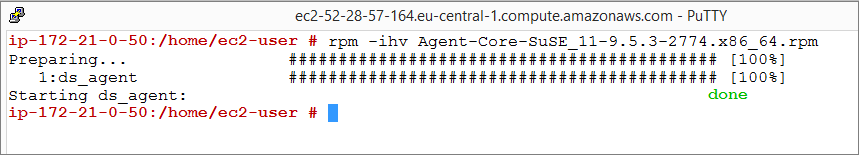 This indicates that the agent installation is complete
This indicates that the agent installation is complete
You can also deploy the agent using a deployment script generated from Server & Workload Protection.
The agent is now installed on the SAP server, but no protection modules are active.
To enable protection, you need to add the SAP server to Server & Workload Protection.
Add the SAP server to Server & Workload Protection and activate the agent
To add the SAP server, open the Server & Workload Protection console and on the Computers tab, click New. There are several ways to add the server, including synchronization with Microsoft
Active Directory, VMware vCenter, Amazon Web Services, or Microsoft Azure. You can
also add the computer using an FQDN or IP address. For details, see About adding computers.
The status of your instance is either Unmanaged (Activation Required) or Unmanaged (Unknown). Next, activate the agent before Server & Workload Protection can assign rules and policies to protect the computer. The activation process includes
the exchange of unique fingerprints between the agent and Server & Workload Protection. There are two ways to activate the agent: agent-initiated or manager-initiated.
Manager-initiated activation: This method requires that Server & Workload Protection (the manager) can connect to the FQDN or the IP of the agent via the agent's listening port number for heartbeats. This can sometimes be difficult due to NAT port forwarding, firewall, or AWS security
groups. To perform manager-initiated activation, go to the Computers tab in the Server & Workload Protection console, right-click the instance where the agent is installed and click . If you use manager-initiated activation, you should also Protect the agent from unauthorized managers.
Agent-initiated activation: The agent-initiated method requires that the agent can
connect to Server & Workload Protection.
You also need to enable agent-initiated activation from the Server & Workload Protection console by clicking and selecting Allow Agent-Initiated Activation.
Next, use a locally-run command-line tool on the agent to initiate the activation
process. The minimum activation instruction contains the activation command and the
Server & Workload Protection URL (including the port number):
dsa_control -a dsm://[managerurl]:[port]/where:
-ais the command to activate the agent, anddsm://managerurl:443/is the parameter that points the agent to Server & Workload Protection. ("managerurl" is the URL of Server & Workload Protection, and "443" is the default agent-to-manager communication port.)
The manager URL is the only required parameter for the activation command. Additional
parameters are also available. For a list of available parameters, see Command-line basics.
To confirm the activation:
- In the Server & Workload Protection console, select the Computers tab.
- Click the computer name, then click Details and check that the computer's status is Managed.
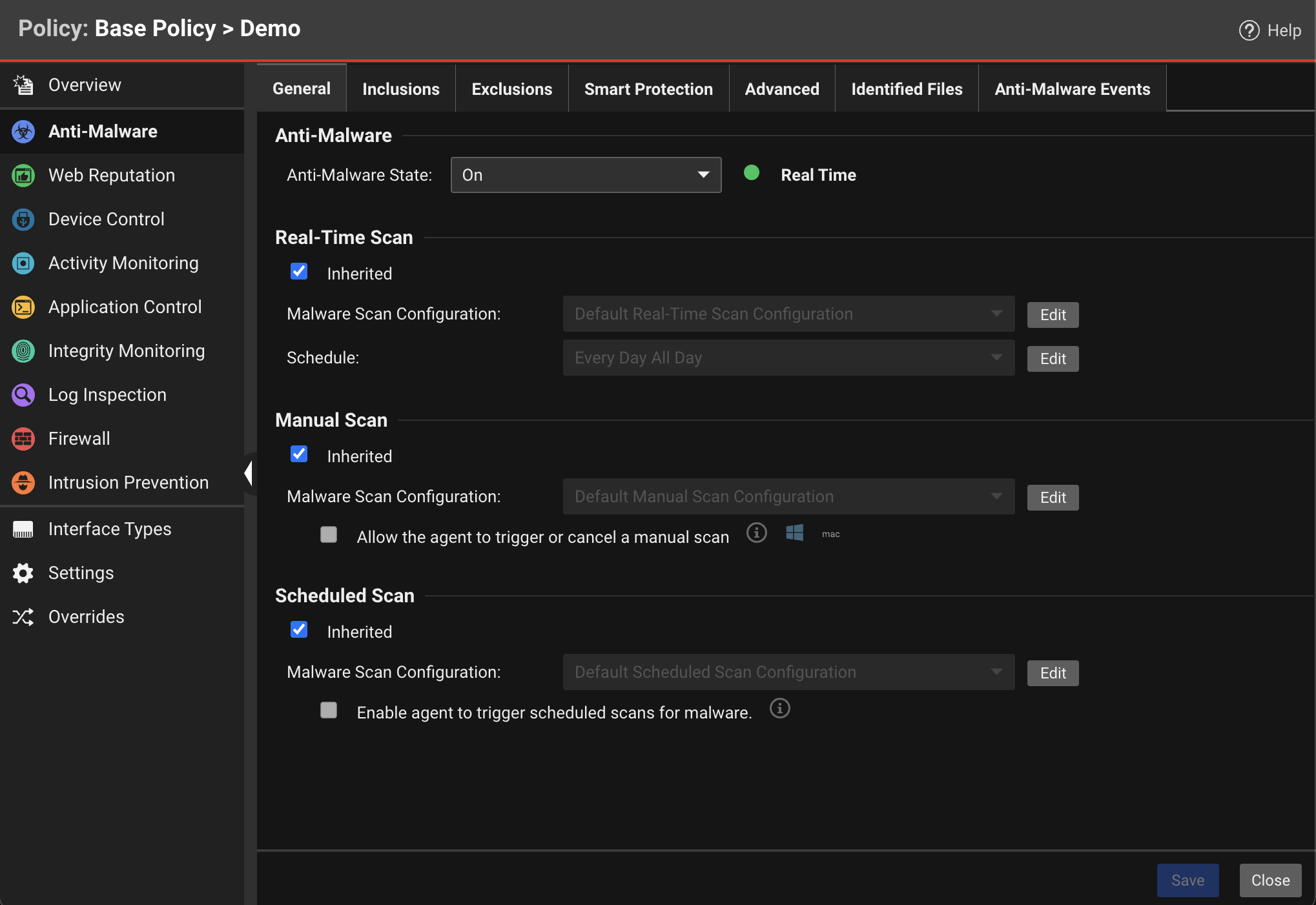
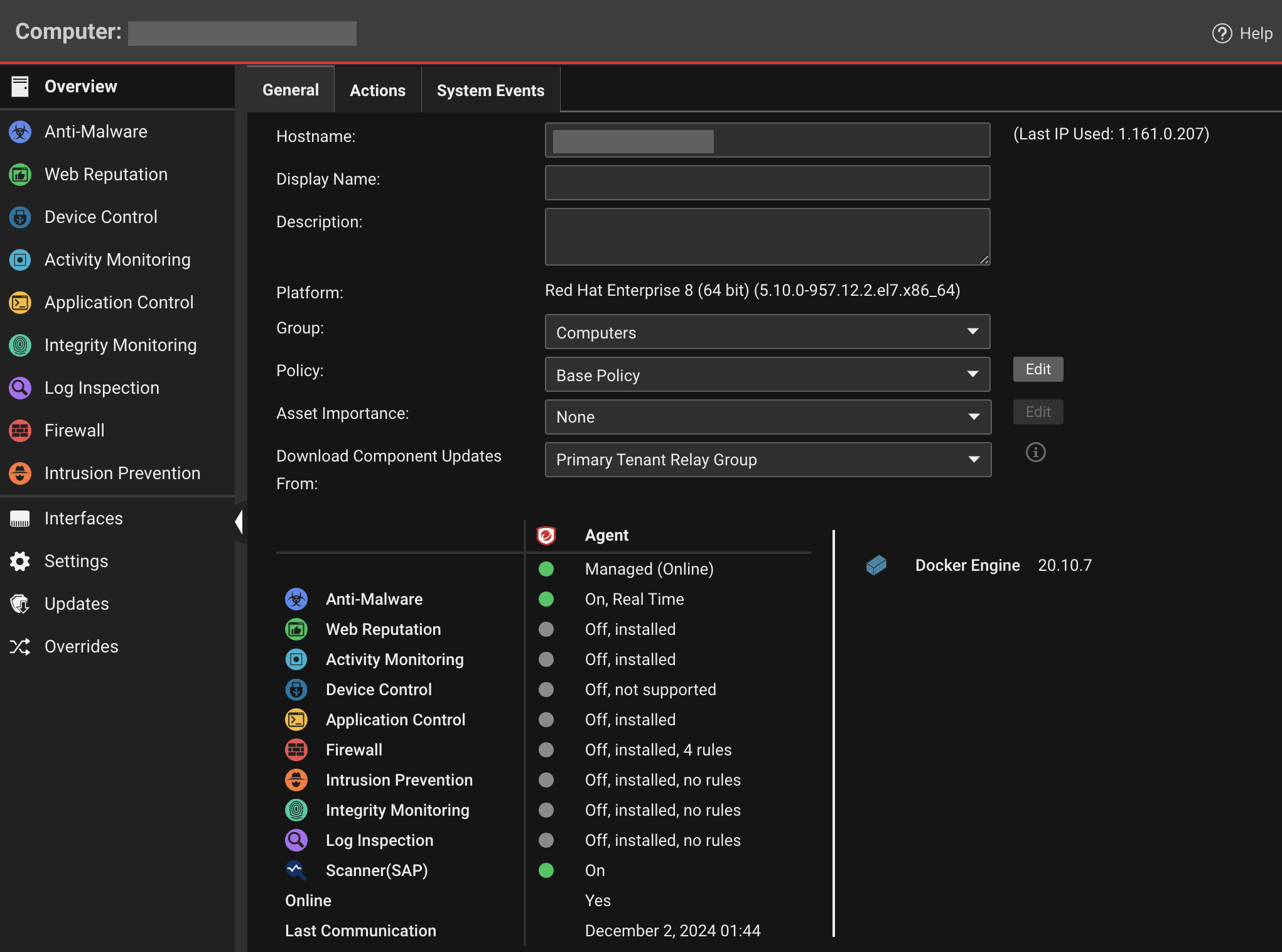
Assign a security profile
At this point, the status of the agent is Managed (Online), but there is no protection module installed. This means that the agent and Server & Workload Protection are communicating but the agent is not using any configuration.
There are several ways to apply protection. In this example, the configuration is
done directly on the SAP instance by activating anti-malware and SAP and assigning
the default Scan Configurations.
-
In the Computer or Policy editor, go to .
-
In the Anti-Malware section, set Configuration to On (or Inherited On), and then click Save.
-
In the Real-Time Scan, Manual Scan, or Scheduled Scan sections, set the Malware Scan Configuration and Schedule, or allow those settings to be inherited from the parent policy.
-
Click Save. The status of the anti-malware module changes to Off, installation pending. This means that the agent is retrieving the required module from Server & Workload Protection. For this to work, the client needs to access the Relay on the relay's listening port number. A few moments later, the agent should start downloading component updates such as anti-malware patterns and scan engines.
-
In the Computer editor, go to .
-
In the SAP section, set Configuration to On (or Inherited On), and then click Save.
After status of the agent changes to Managed (Online) again and the anti-malware and Scanner (SAP) modules are On, you can proceed with the SAP configuration.
Configure SAP to use the agent
The agent is now running and can scan the file system of its operating system. Next,
make the agent aware of the SAP application server. To use this, create a virus scan
adapter inside the application server. The virus scan adapter must be part of a group.
After the virus scan adapter and virus scan group are created, you can use virus scan
profiles to configure what to scan and how to behave.
Perform the following:
The virus scan group and the virus scan adapter are both global configurations (client
00). The virus scan profile must be configured in each tenant (client 01, 02, and
so on).
Configure the scanner group
-
In the SAP WinGUI, run the VSCANGROUP transaction. In Edit mode, click New Entries.
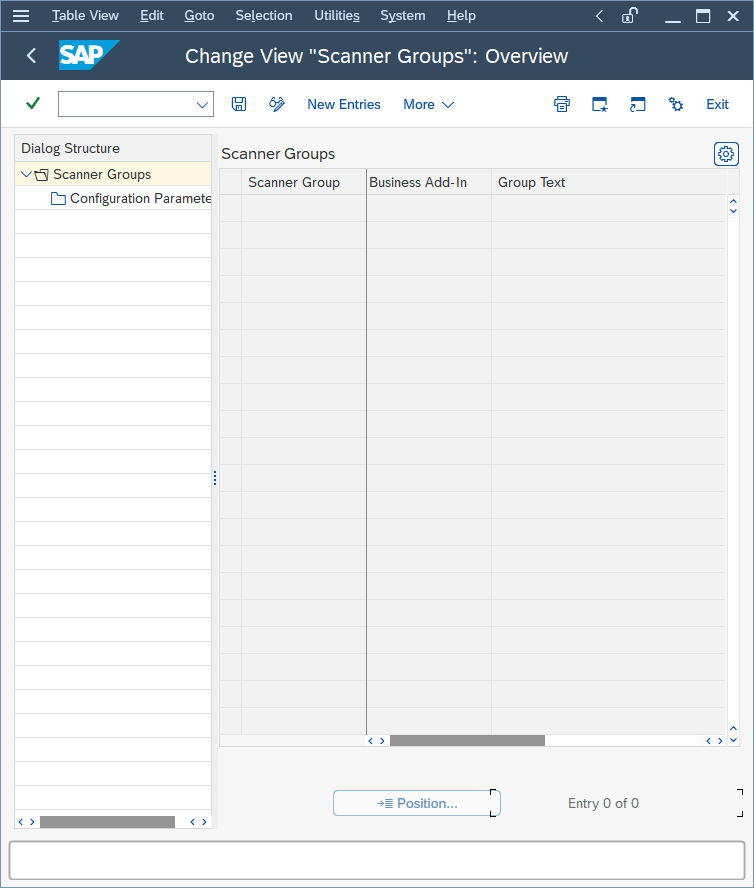
-
Create a new scanner group, specifying a group name in the Scanner Group area and a description of the scanner group in the Group Text area.
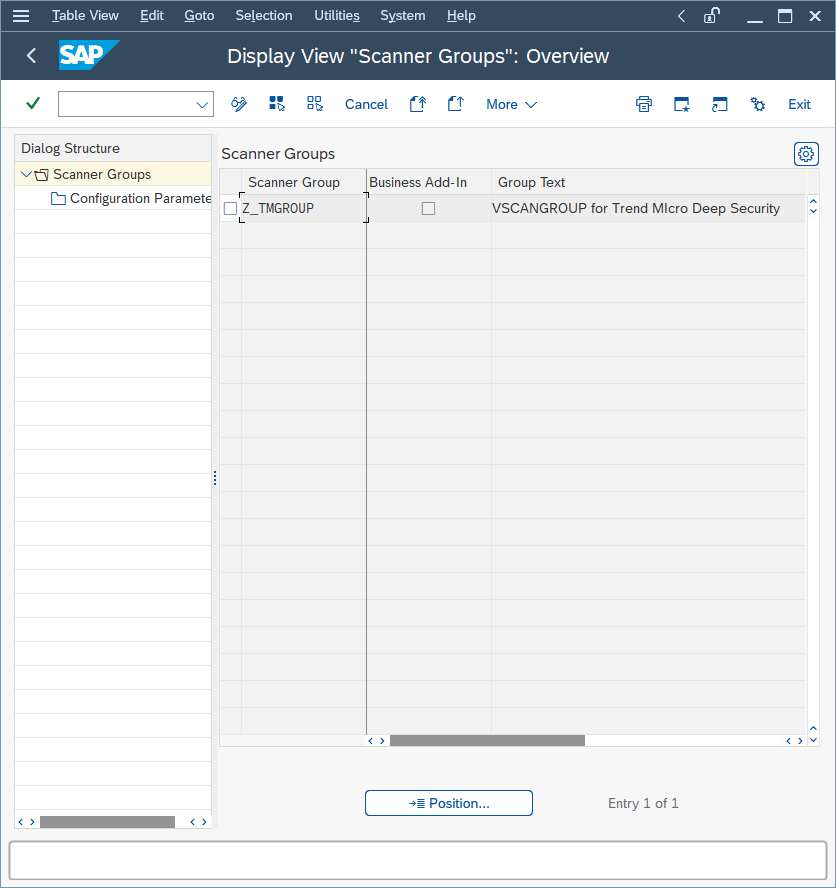
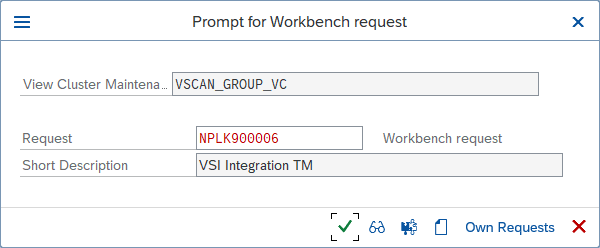
-
Click Save or leave the edit mode.A dialog named Prompt for Workbench request appears. In the following example, a new workbench request is created to keep track of all the VSI-related changes:
The next step is the actual configuration of the VSI integration. It is called Virus Scan Adapter.
Configure the virus scan provider
-
In the SAP WinGUI, run the VSCAN transaction. In Edit mode, click New Entries.
-
Enter a configuration for a VSI-certified solution.In the following example, a number of configuration parameters are set:
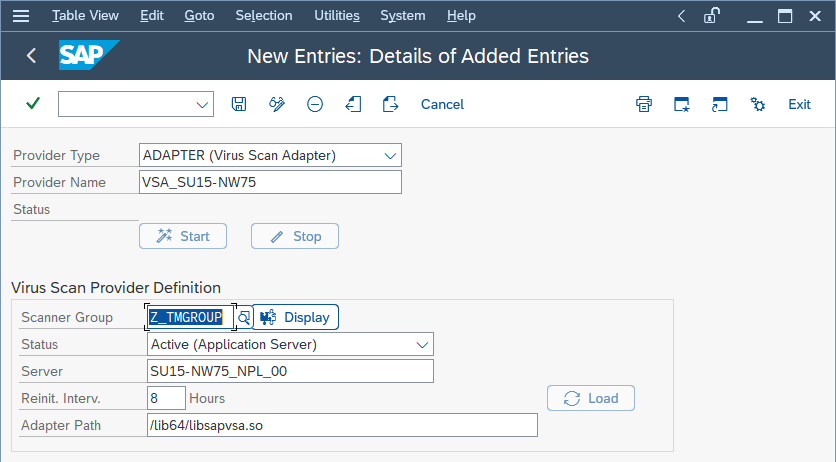 SettingValueDescriptionProvider TypeADAPTER (Virus Scan Adapter)Automatically set (default)Provider NameVSA_<host name>Automatically set, serves as aliasScanner GroupSelect the group that you configured earlierAll previously created scanner groups, which you can display using the input helpStatusActive (Application Server)Automatically set (default)Servernplhost_NPL_42Automatically set, hostnameReinit. Interv.8 HoursSpecifies the number of hours after which the Virus Scan Adapter is reinitialized and load new virus definitions.Adapter Path (Linux)/lib64/libsapvsa.soDefault pathAdapter Path (Windows)C:\Program Files\TrendAI™\Deep Security Agent\lib\dsvsa.dllDefault path
SettingValueDescriptionProvider TypeADAPTER (Virus Scan Adapter)Automatically set (default)Provider NameVSA_<host name>Automatically set, serves as aliasScanner GroupSelect the group that you configured earlierAll previously created scanner groups, which you can display using the input helpStatusActive (Application Server)Automatically set (default)Servernplhost_NPL_42Automatically set, hostnameReinit. Interv.8 HoursSpecifies the number of hours after which the Virus Scan Adapter is reinitialized and load new virus definitions.Adapter Path (Linux)/lib64/libsapvsa.soDefault pathAdapter Path (Windows)C:\Program Files\TrendAI™\Deep Security Agent\lib\dsvsa.dllDefault path -
Click Save or leave the edit mode.A prompt to pack this into a workbench request appears.
-
Confirm the request, then click Start.The Status light turns green, which means the adapter is loaded and active.
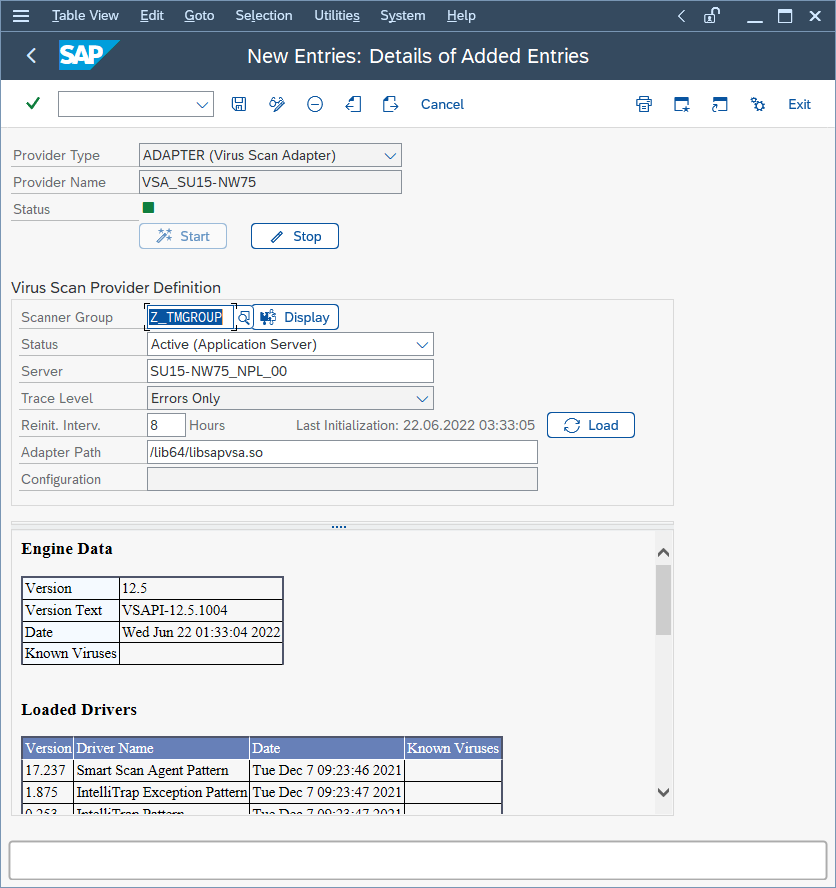
At this point, the VSI configuration is nearly finished. The application server is
now ready to process file transactions using a virus scan provided by TrendAI™.
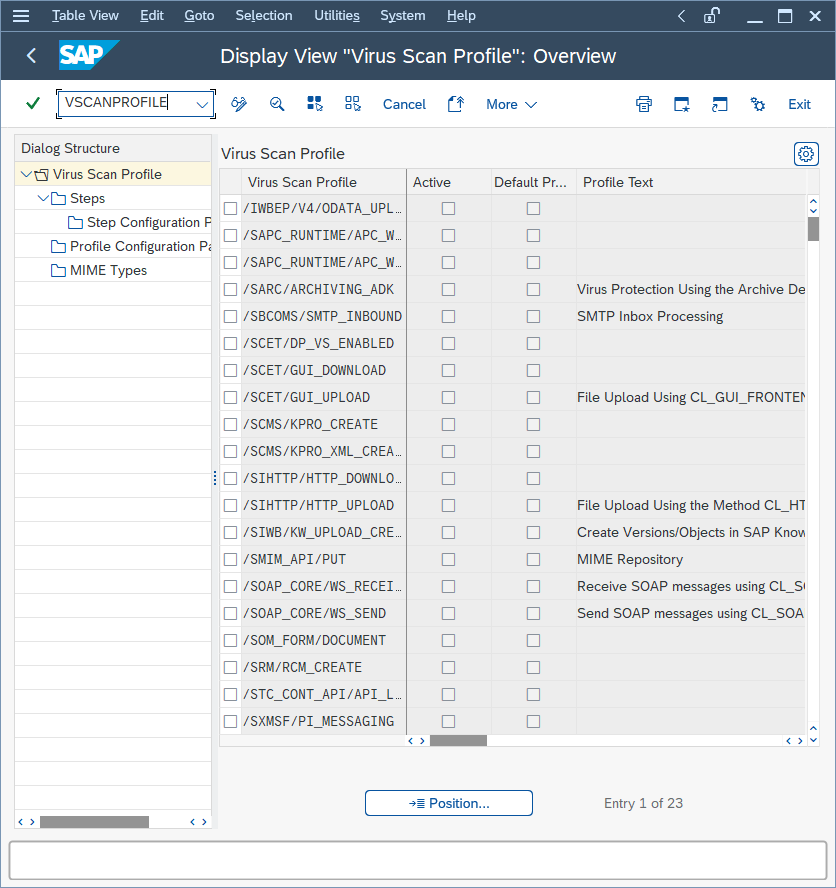
Configure the virus scan profile
-
In the SAP WinGUI, run the VSCANPROFILE transaction, then select the SAP operation that requires virus scan.For example, select Active for /SCET/GUI_UPLOAD or /SCET/GUI_DOWNLOAD, and then click Save.
-
In edit mode, click New Entries.The virus scan profiles define how specific transactions (file uploads, file downloads, and so on) are handled corresponding to the virus scan interface. To use the previously configured virus scan adapter in the application server, you need to create a new virus scan profile.
-
In Scan Profile, enter Z_TMProfile and select Active, Default Profile, and Evaluate Profile Configuration Param.
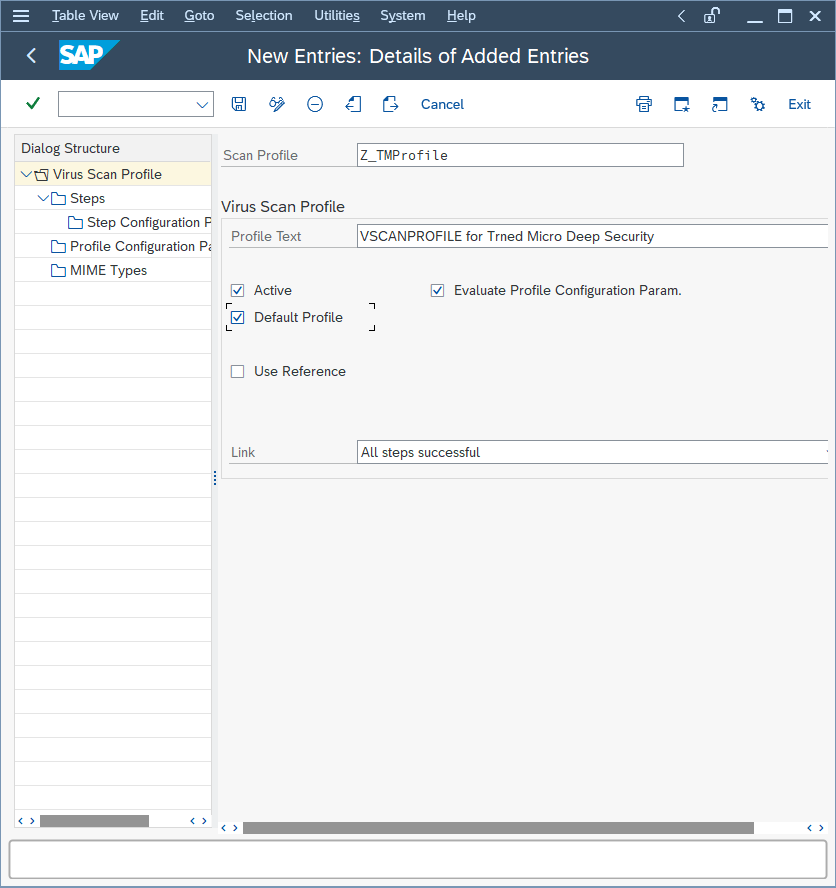
-
While still in edit mode, double-click Steps to configure the steps:
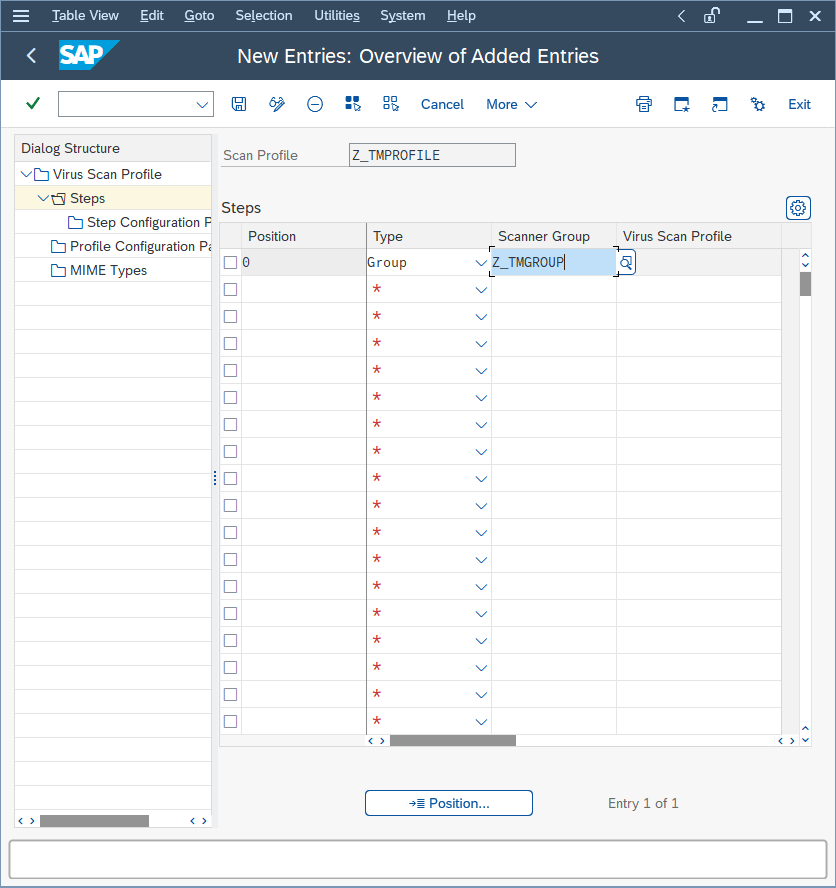
-
Click New Entries.The steps define what to do when the profile is called by a transaction.
-
Set Position to 0, Type to Group, and Scanner Group to the name of the group that you configured earlier.
-
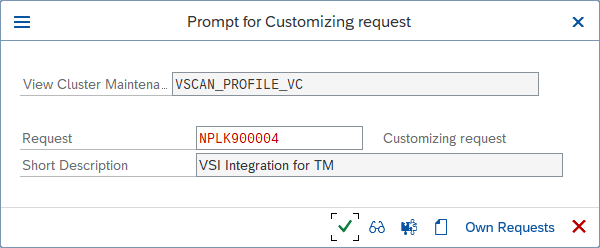
Click Save or leave the edit mode.A notification eventually appears about an existing virus scan profile, /SCET/DP_VS_ENABLED.
-
Ignore the notification about an existing profile because the profile is not active and is not used.After confirming this notification, you are asked to pack this configuration in a customization request. Creating a new request helps keep track of the changes that have been made:
-
To create configuration parameters for a step, double-click Profile Configuration Parameters, then click New Entries and set the parameters:ParameterTypeDescriptionCUST_ACTIVE_CONTENTBOOLCheck if a file contains script (JavaScript, PHP, ASP script) and block.CUST_CHECK_MIME_TYPEBOOL
Check if the file extension name matches its MIME type. If they do not match, the file is blocked. All MIME types and extension names can be exactly matched. For example: - Word files must be .doc or .dot
- JPEG files must be .jpg
- Text and binary files could be any extension (do not block)
See Supported MIME types for the built-in mapping table. To configure the scanner to recognize MIME types or file extensions that the built-in table does not include, see Add custom MIME type mappings. -
Double-click Step Configuration Parameters. Click New Entries and set the parameters:ParameterTypeDescriptionDefault on LinuxDefault on WindowsSCANBESTEFFORTBOOLThe scan should be performed on the best effort basis; that is, all security critical flags that allow a VSA to scan an object should be activated, such as SCANALLFILES and SCANEXTRACT, but also internal flags. Details about exactly which flags these are can be stored in the certification.not setnot setSCANALLFILESBOOLScans for all files regardless of their file extension.disableddisabledSCANEXTENSIONSCHARList of the file extensions for which the VSA should scan. Only files with the configured extensions are checked. Other extensions are blocked. Wildcards can also be used here to search for patterns. \* stands for this location and following and ? stands for only this character. For example, exe;com;do?;ht* => \`\*\` means to scan all files.null""SCANLIMITINTThis setting applies to compressed files. It specifies the maximum number of files to unpack and scan.INT_MAX65535SCANEXTRACTBOOLArchives or compressed objects are to be unpackedenabledenabledSCANEXTRACT_SIZESIZE_TMaximum unpack size0x7FFFFFFF62914560 (60 MB)SCANEXTRACT_DEPTHINTMaximum depth to which an object is to be unpacked.2020SCANLOGPATHCHARCustom log path for VSAMust be an absolute path to either a regular file or to a location where a regular file can be created. Cannot be an executable file path. Only limited log messages are written. For example, the detected malware.Supported by agent versions released May 2, 2024, and later.(not set)(not set)SCANMIMETYPESCHARList of the MIME types for which to scan. Only files with configured MIME types are checked. Other MIME types are blocked. This parameter works only if CUST_CHECK_MIME_TYPE is enabled.not setnot setBLOCKMIMETYPESCHARList of MIME types to block. This parameter works only if CUST_CHECK_MIME_TYPE is enabled.not setnot setBLOCKEXTENSIONSCHARList of file extensions to block.not setnot set
This configuration is per-client, so it must be done in each tenant of the SAP application
server.
Add custom MIME type mappings
The SAP Scanner uses a built-in mapping table that allows you to associate each recognized
MIME type with one or more accepted file extensions. When the
CUST_CHECK_MIME_TYPE parameter is enabled, the scanner determines the actual MIME type of each uploaded
file, locates that MIME type in the table, and blocks the file unless its extension
is listed for that MIME type. For the contents of the built-in table, see Supported MIME types.The built-in table does not recognize MIME types or file extensions that are
specific to your organization, including proprietary formats and files that use
customized extensions. As a result, those files are blocked as MIME type
mismatches whenever
CUST_CHECK_MIME_TYPE is enabled. To prevent
these unwanted blocks without disabling the MIME type check or upgrading the
agent, supplement the built-in table with custom entries. Custom entries add to
the built-in table; they do not replace any of its existing entries.Custom MIME type mappings are supported on Linux SAP application servers only. They
have no effect on Windows agents.
You can configure custom entries through either of the following sources:
- Policy (recommended): Entries are defined in the Server & Workload Protection console and applied to every SAP server protected by the policy.
- Local INI file: Entries are defined directly on a single SAP server. Use this method to override the policy on a specific host, or to apply an entry before the agent receives the updated policy.
When both sources define entries for the same MIME type, the local INI entry
replaces the policy entry on that server. Entries for other MIME types continue
to be drawn from whichever source defines them.
Configuration through policy
-
In Server & Workload Protection, open the Computer or Policy editor and go to .
-
In the SAP area, locate Custom MIME type mappings and add one entry for each MIME type that you want the scanner to recognize. For each entry, provide the following values:
- MIME type: The complete MIME type string, for
example,
application/x-custom. - File extensions: A comma-separated list of one
or more extensions to associate with the MIME type, specified without
leading dots. Extensions are matched case-insensitively. For example,
cst, custom.
- MIME type: The complete MIME type string, for
example,
-
Click Save. Server & Workload Protection validates each entry and rejects any entry that has an empty MIME type or an empty extension list. Valid entries are distributed to the agent at the next heartbeat and are merged with the built-in mapping table that the SAP Scanner uses.
The agent stores the resulting policy configuration at
/var/opt/ds_agent/guests/0000-0000-0000/amvmcfg.xml in the
following form:<CustomMimeMappings> <CustomMimeMapping mimeType="application/x-custom" extensions=";cst;custom;"/> <CustomMimeMapping mimeType="application/vnd.company" extensions=";comp;"/> <CustomMimeMapping mimeType="text/x-specialformat" extensions=";spc;special;"/> </CustomMimeMappings>
Do not edit
amvmcfg.xml directly. The agent regenerates the file each time it receives a policy update, and
any manual modifications are overwritten.Configuration through a local INI file
Use the local INI file when you need to override the policy on a single SAP
server, or to apply an entry before the agent receives the updated policy.
-
On the SAP server, create or edit the file
/var/opt/ds_agent/am/custom_mime.ini. -
Add each mapping on its own line, using the following syntax:
<mime-type>=;<extension1>;<extension2>;…
For example:application/x-custom=;cst;custom; application/vnd.company=;comp; text/x-specialformat=;spc;special;
The file must conform to the following format requirements:- One mapping per line, with no section headers. The file format
differs from
dt.ini. - A semicolon at the start of the extension list, between consecutive extensions, and at the end of the list.
- Extensions specified without leading dots. Extensions are matched case-insensitively.
- One mapping per line, with no section headers. The file format
differs from
-
Save the file. The agent applies the new entries the next time it receives a scan request. Restarting the agent is not required.
ImportantWhen the same MIME type is defined in both the local INI
file and the policy, the local INI entry replaces the policy entry on that
server. All other policy-defined entries remain in effect.
|
Evaluation order
When
CUST_CHECK_MIME_TYPE is enabled, the SAP Scanner determines
the actual MIME type of each uploaded file and then verifies the file's
extension against the available mapping sources in the following order:- The scanner first consults the built-in mapping table. If the file's MIME type is present in the built-in table and the file's extension is listed for that MIME type, the file is allowed to pass to the next scan stage.
- If the file's MIME type is not present in the built-in table, the scanner consults the custom mappings: first the local INI file, then the policy. If the file's extension is listed for the detected MIME type in either source, the file is allowed to pass.
- If no source recognizes the combination of MIME type and extension, the scanner blocks the file.
Invalid custom entries—those with an empty MIME type, a malformed extension list,
or a duplicate definition within the same source—are recorded in
/var/opt/ds_agent/diag/ds_am.log and disregarded. The
remaining valid entries continue to apply.Troubleshooting
-
To verify that the agent has received the policy-defined entries, examine
/var/opt/ds_agent/guests/0000-0000-0000/amvmcfg.xmlon the SAP server. The file should contain a<CustomMimeMappings>element that lists each of your entries. -
To verify that the local INI file is being read, search
/var/opt/ds_agent/diag/ds_am.logfor entries that referencecustom_mime.ini. -
If a file continues to be blocked after you have added a custom mapping for it, run the SAP transaction VSCANTEST and review the Content Information output. The MIME type that the scanner detected must match the
mimeTypevalue in your mapping exactly. The scanner does not normalize casing or trim surrounding whitespace, so any discrepancy prevents the entry from taking effect.
Test the virus scan interface
-
In the SAP WinGUI, run the VSCANTEST transaction.
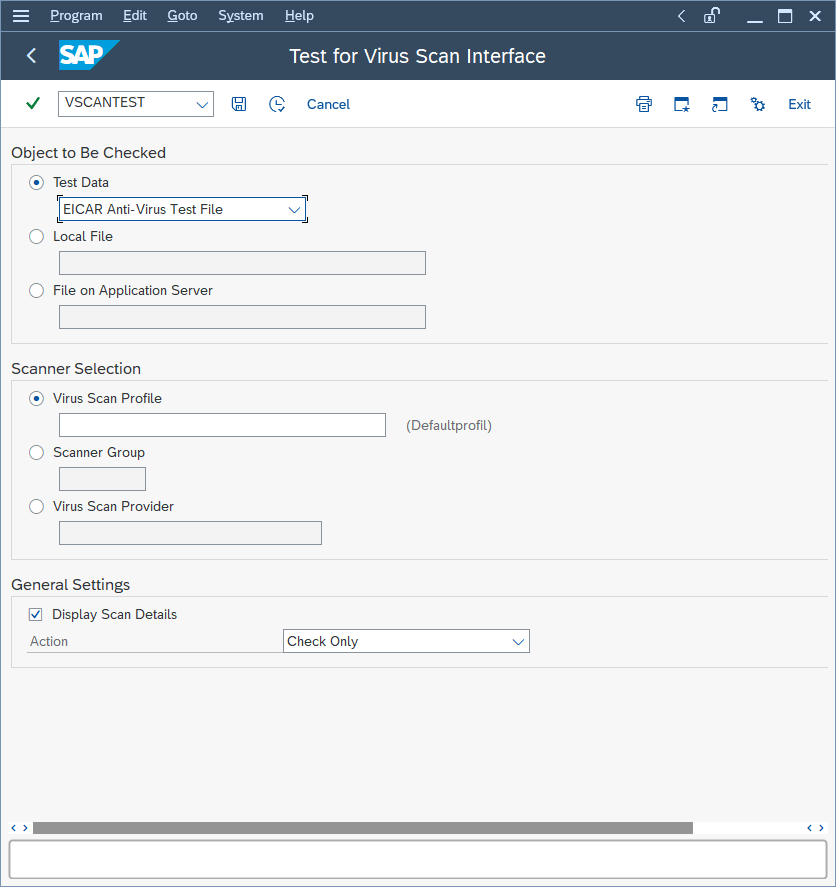 Every VSI-aware SAP application server also has a built-in test to check whether the configuration steps were done correctly. For this, an EICAR test virus (www.eicar.org) is packed in a transaction that can call a specific scanner.
Every VSI-aware SAP application server also has a built-in test to check whether the configuration steps were done correctly. For this, an EICAR test virus (www.eicar.org) is packed in a transaction that can call a specific scanner. -
If you do not fill in anything, the default profile is called, which was configured in the last step, so do not fill in anything.
-
Click Execute.A notification appears that explains what an EICAR test virus is.
-
Confirm the notification.The transaction is intercepted:
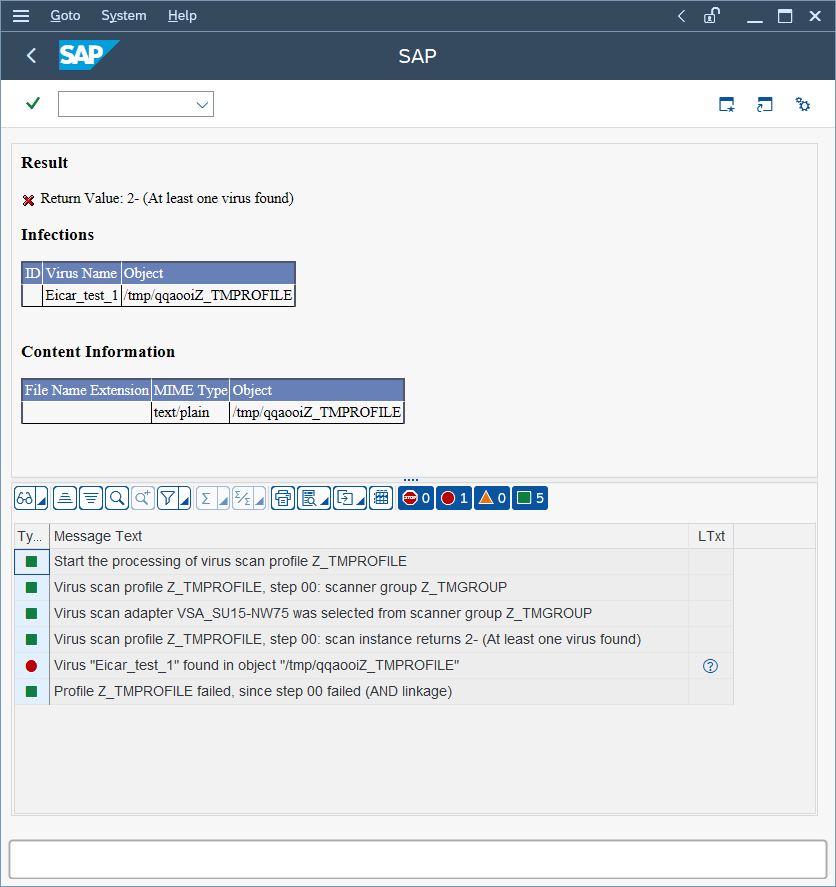
Infections shows information about the detected malware.
Content Information shows the correct MIME-type of the file.
The file name is always a randomly generated 7-letter alphabetic string followed by
the virus scan profile name.
After this, there is an output about each step of the transaction:
- The transaction called the default virus scan profile, which is the virus scan profile Z_TMPROFILE.
- The virus scan profile Z_TMPROFILE is configured to call an adapter from the virus scan group Z_TMGROUP.
- The virus scan group Z_TMGROUP has multiple adapters configured and calls one of them (in this case, VSA_NPLHOST).
- The virus scan adapter returns value 2-, which means a virus was found.
- Information about the detected malware is displayed by showing Eicar_test_1 and the file object /tmp/ zUeEbZZ_TMPROFILE.
- The called default virus scan profile Z_TMPROFILE fails because step 00 (the virus scan group) was not successful and therefore the file transaction is stopped from further processing.
For a cross-check, there is also information about this malware event in the Server & Workload Protection console. To see the event, open the Computer editor and click .
Supported MIME types
The MIME types supported by the Scanner vary depending on which version of the agent
you are using.
To configure the scanner to recognize MIME types or file extensions that this
table does not include, without upgrading the agent, see Add custom MIME type
mappings.
- Agent version 9.6 uses VSAPI 9.85
- Agent version 10.0 uses ATSE 9.861
- Agent version 10.1 uses ATSE 9.862
- Agent version 10.2, 10.3, 11.0, 11.1, and 11.2 uses ATSE 10.000
- Agent version 11.3 and higher uses ATSE 11.0.000
|
MIME type
|
Description
|
Extension
|
Supported in 9.6 agent
|
Supported in 10.0 agent
|
Supported in 10.1 agent and later
|
|
application/octet-stream
|
|
*
|
Yes
|
Yes
|
Yes
|
|
application/com
|
COM File
|
com
|
Yes
|
Yes
|
Yes
|
|
application/ecmascript
|
EMCScript File
|
es
|
Yes
|
Yes
|
Yes
|
|
application/hta
|
HTA File
|
hta
|
Yes
|
Yes
|
Yes
|
|
application/java-archive
|
Java Archive (JAR) file
|
jar
|
Yes
|
Yes
|
Yes
|
|
application/javascript
|
Javascript File
|
js, jsxinc, jsx
|
Yes
|
Yes
|
Yes
|
|
application/msword
|
Word for Windows
|
doc, dot
|
Yes
|
Yes
|
Yes
|
|
application/vnd.ms-access
|
MS Access
|
mdb
|
No
|
No
|
No
|
|
application/vnd.ms-project
|
MS Project
|
mpp
|
No
|
No
|
No
|
|
application/msword
|
MS Word
|
doc, dot
|
Yes
|
Yes
|
Yes
|
|
application/octet-stream
|
COM File
|
com
|
Yes
|
Yes
|
Yes
|
|
application/octet-stream
|
EXE File
|
exe
|
Yes
|
Yes
|
Yes
|
|
application/pdf
|
Adobe Portable Document Format file
|
pdf
|
Yes
|
Yes
|
Yes
|
|
application/postscript
|
Postscript
|
ai
|
Yes
|
Yes
|
Yes
|
|
application/postscript
|
Postscript
|
ps
|
Yes
|
Yes
|
Yes
|
|
application/postscript
|
Postscript
|
ps
|
Yes
|
Yes
|
Yes
|
|
application/rar
|
RAR File
|
rar
|
Yes
|
Yes
|
Yes
|
|
application/rtf
|
Microsoft RTF
|
rtf
|
Yes
|
Yes
|
Yes
|
|
application/sar
|
Sar File
|
sar
|
Yes
|
Yes
|
Yes
|
|
application/vnd.ms-excel
|
Excel for Windows
|
xls, xlt, xla
|
Yes
|
Yes
|
Yes
|
|
application/vnd.ms-outlook
|
Outlook for Windows
|
msg
|
No
|
Yes
|
Yes
|
|
application/vnd.ms-powerpoint
|
Windows PowerPoint
|
ppt, pot, pps, ppa
|
Yes
|
Yes
|
Yes
|
|
application/vnd.ms-publisher
|
MS Publisher
|
pub
|
No
|
No
|
Yes
|
|
application/vnd.oasis.opendocument
|
Open Document
|
odf
|
Yes
|
Yes
|
Yes
|
|
application/vnd.openxmlformats-officedocument.presentationml.presentation
|
MS Office File
|
pptx, potx, ppsx, ppam, pptm, potm, ppsm
|
Yes
|
Yes
|
Yes
|
|
application/vnd.openxmlformats-officedocument.spreadsheetml.sheet
|
MS Office File
|
xlsx, xltx, xlsm, xltm, xlam, xlsb
|
Yes
|
Yes
|
Yes
|
|
application/vnd.openxmlformats-officedocument.wordprocessingml.document
|
MS Office File
|
docx, dotx, docm, dotm
|
Yes
|
Yes
|
Yes
|
|
application/vnd.rn-realmedia
|
Real Media
|
rm
|
Yes
|
Yes
|
Yes
|
|
application/wordperfect
|
WOrdPerfect
|
wp, wp5, wp6, wpd, w60, w61
|
Yes
|
Yes
|
Yes
|
|
application/x-alf
|
|
alf
|
Yes
|
Yes
|
Yes
|
|
application/x-arc-compressed
|
ARC File
|
arc
|
Yes
|
Yes
|
Yes
|
|
application/x-bzip2
|
bZIP File
|
*
|
Yes
|
Yes
|
Yes
|
|
application/x-cpio
|
CPIO File
|
*
|
Yes
|
Yes
|
Yes
|
|
application/x-director
|
Macromedia Director Shockwave Movie
|
dcr
|
Yes
|
Yes
|
Yes
|
|
application/x-gzip
|
Gzip
|
*
|
Yes
|
Yes
|
Yes
|
|
application/xhtml+xml
|
XHTML
|
dhtm, dhtml, htm, html, htx, sht, shtm, shtml, stml, xht, xhtm, xhtml, xml, txt
|
Yes
|
Yes
|
Yes
|
|
application/x-java-class
|
JAVA Applet
|
class
|
Yes
|
Yes
|
Yes
|
|
application/x-kep
|
|
kep
|
Yes
|
Yes
|
Yes
|
|
application/x-otf
|
|
otf
|
Yes
|
Yes
|
Yes
|
|
application/x-sapshortcut
|
|
sap, sapc
|
Yes
|
Yes
|
Yes
|
|
application/x-shockwave-flash
|
Macromedia Flash
|
swf
|
Yes
|
Yes
|
Yes
|
|
application/x-silverlight-app
|
PKZIP
|
xap
|
Yes
|
Yes
|
Yes
|
|
application/x-sim
|
|
sim
|
Yes
|
Yes
|
Yes
|
|
application/x-tar
|
TAR File
|
tar
|
Yes
|
Yes
|
Yes
|
|
application/x-vbs
|
|
*
|
Yes
|
Yes
|
Yes
|
|
application/zip
|
ZIP File
|
zip, zipx
|
Yes
|
Yes
|
Yes
|
|
audio/basic
|
Audio
|
snd, au
|
Yes
|
Yes
|
Yes
|
|
audio/midi
|
MIDI
|
mid, midi, rmi, mdi, kar
|
Yes
|
Yes
|
Yes
|
|
audio/x-aiff
|
Audio InterChange File Format from Apple/SGI
|
aiff, aif, aifc
|
Yes
|
Yes
|
Yes
|
|
audio/x-mpeg-3
|
MP3
|
mp3
|
Yes
|
Yes
|
Yes
|
|
audio/x-realaudio
|
Real Audio
|
ra
|
Yes
|
Yes
|
Yes
|
|
audio/x-voc
|
Creative Voice Format(VOC)
|
voc
|
Yes
|
Yes
|
Yes
|
|
image/bmp
|
Windows BMP
|
bmp
|
Yes
|
Yes
|
Yes
|
|
image/gif
|
GIF
|
gif
|
Yes
|
Yes
|
Yes
|
|
image/ico
|
Windows Icon
|
ico
|
Yes
|
Yes
|
Yes
|
|
image/jpeg
|
JPEG
|
jpg, jpeg, jpe, jif, jfif, jfi
|
Yes
|
Yes
|
Yes
|
|
image/msp
|
Microsoft Paint
|
msp
|
Yes
|
Yes
|
Yes
|
|
image/png
|
Portable Network Graphics
|
png
|
Yes
|
Yes
|
Yes
|
|
image/ppm
|
PPM image
|
ppm
|
Yes
|
Yes
|
Yes
|
|
image/svg+xml
|
|
svg
|
Yes
|
Yes
|
Yes
|
|
image/tiff
|
TIFF
|
tif, tiff
|
Yes
|
Yes
|
Yes
|
|
image/vnd.ms-modi
|
Microsoft Document Imaging
|
mdi
|
Yes
|
Yes
|
Yes
|
|
image/x-cpt
|
Corel PhotoPaint
|
cpt
|
Yes
|
Yes
|
Yes
|
|
image/x-pcx
|
PCX
|
pcx
|
Yes
|
Yes
|
Yes
|
|
image/x-pict
|
Macintosh Bitmap
|
pct
|
Yes
|
Yes
|
Yes
|
|
image/x-ras
|
Sun Raster(RAS)
|
ras
|
Yes
|
Yes
|
Yes
|
|
image/x-wmf
|
Windows Metafile
|
wmf
|
Yes
|
Yes
|
Yes
|
|
text/csv
|
CSV
|
csv, txt
|
Yes
|
Yes
|
Yes
|
|
text/html
|
HTML
|
dhtm, dhtml, htm, html, htx, sht, shtm, shtml, stml, xht, xhtm, xhtml, xml, txt
|
Yes
|
Yes
|
Yes
|
|
text/plain
|
|
*
|
Yes
|
Yes
|
Yes
|
|
text/plain
|
Text File
|
txt
|
Yes
|
Yes
|
Yes
|
|
text/xml
|
XML
|
dhtm, dhtml, htm, html, htx, sht, shtm, shtml, stml, xht, xhtm, xhtml, xml, txt
|
Yes
|
Yes
|
Yes
|
|
text/xsl
|
XSL
|
xsl
|
Yes
|
Yes
|
Yes
|
|
unknown/unknown
|
|
*
|
Yes
|
Yes
|
Yes
|
|
video/mpeg
|
|
*
|
Yes
|
Yes
|
Yes
|
|
video/quicktime
|
Quick Time Media
|
qt
|
Yes
|
Yes
|
Yes
|
|
video/x-fli
|
AutoDesk Animator
|
fli
|
Yes
|
Yes
|
Yes
|
|
video/x-flv
|
Macromedia Flash FLV Video
|
flv
|
Yes
|
Yes
|
Yes
|
|
video/x-ms-asf
|
Advanced Streaming Format
|
asf
|
Yes
|
Yes
|
Yes
|
|
video/x-scm
|
Lotus ScreenCam Movie
|
scm
|
Yes
|
Yes
|
Yes
|
|
text/x-msdos-batch
|
A batch file is a script file in DOS, OS/2, and Microsoft Windows
|
bat, cmd, btm, txt
|
No
|
No
|
No
|


