Learn about the security control family implementation levels used in the Cyber Risk Quantification business self-assessment.
Security control implementation levels describe how well your organization's security
controls meet the requirements of each NIST SP 800-53 control family. For each control
family in the Security practices tab of the advanced business self-assessment, select the level that best describes
your current practices.
Answers determine how effectively your security controls reduce both the likelihood
of a successful attack and the financial impact if an incident occurs. More complete
answers, including those provided automatically by connected data sources, produce
results with higher confidence levels.
Some security practice questions can be automatically answered when applicable data
is available from a connected data source. Automatic answers are available when a
data source is connected and the control is applicable to the assets being analyzed
in the selected asset group. If data from a connected data source is available for
a control, the data source answer overrides any manually selected implementation level
for that control.
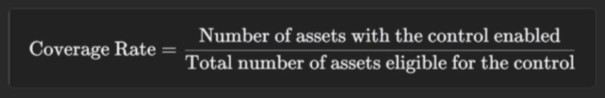
The implementation level is calculated from the control's coverage rate. The coverage
rate is the proportion of eligible assets in the selected asset group that have the
control actively enabled. Ineligible assets are assets that cannot support the control
due to technical, architectural, or functional constraints. Automatically answered
questions use this coverage rate to determine the implementation level of a given
security practice. You can also use the coverage rate as a general guideline when
answering questions manually.
Use the following table to identify the implementation level that best describes your
current practices for each NIST SP 800-53 security control:
|
Coverage rate
|
Level
|
Description
|
|
0% to 20%
|
1 - Incomplete
|
Few to no related security controls in place.
|
|
21% to 40%
|
2 - Basic
|
Some related security controls in place with basic procedures or a limited scope.
|
|
41% to 60%
|
3 - Functional
|
Related security controls globally established but not necessarily consistently enforced.
|
|
61% to 80%
|
4 - Comprehensive
|
Related security controls globally implemented and monitored.
|
|
81% to 100%
|
5 - Advanced
|
Dynamic, proactive security controls fully integrated into business operations.
|
The following sections describe implementation levels for each NIST SP 800-53 control
family included in the Cyber Risk Quantification security practices assessment.
The AC - Access Control NIST SP 800-53 control family covers managing user account privileges and controlling
account access to systems and information.
The following AC - Access Control controls are included in the Cyber Risk Quantification
security practices assessment:
-
AC-2 Account Management
-
AC-3 Access Enforcement
-
AC-4 Information Flow Enforcement
-
AC-5 Separation of Duties
-
AC-6 Least Privilege
-
AC-7 Unsuccessful Logon Attempts
-
AC-8 System Use Notification
-
AC-10 Concurrent Session Control
-
AC-11 Device Lock
-
AC-12 Session Termination
-
AC-14 Permitted Actions Without Identification or Authentication
-
AC-16 Security and Privacy Attributes
-
AC-17 Remote Access
-
AC-18 Wireless Access
-
AC-19 Access Control for Mobile Devices
-
AC-20 Use of External Systems
-
AC-21 Information Sharing
-
AC-23 Data Mining Protection
The following table describes implementation levels for the AC - Access Control control
family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No formal user access policies in place. Accounts created as needed, permissions inconsistently
assigned, no user activity monitoring.
|
|
2 - Basic
|
Documented user access policy in place requiring unique user IDs. Account creation/deletion
process based on employment status, permissions assigned based on job role.
|
|
3 - Functional
|
Role-based access control (RBAC) implemented to enforce least-privilege principles.
Access logged and occasionally reviewed manually.
|
|
4 - Comprehensive
|
Centralized identity and access management (IAM) system in place across the organization.
Access policies automatically reviewed and updated based on activity monitoring, with
notifications triggered for all account changes.
|
|
5 - Advanced
|
All user identities dynamically verified on access, regardless of privilege, following
a zero-trust architecture. Automated behavioral analytics engines constantly monitor
access activity for unusual behavior.
|
The CA - Assessment, Authorization, and Monitoring NIST SP 800-53 control family covers selecting, implementing, maintaining, and improving
security systems and privacy controls.
The following CA - Assessment, Authorization, and Monitoring controls are included
in the Cyber Risk Quantification security practices assessment:
-
CA-2 Control Assessments
-
CA-3 Information Exchange
-
CA-7 Continuous Monitoring
-
CA-8 Penetration Testing
The following table describes implementation levels for the CA - Assessment, Authorization,
and Monitoring control family in the Cyber Risk Quantification security practices
assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No security assessment or authorization process in place. Security events handled
as they arise, with no formal procedures or monitoring.
|
|
2 - Basic
|
Manual security assessments occasionally performed with basic documentation and reporting.
No standardized scope for security assessments.
|
|
3 - Functional
|
Formal security assessments performed regularly with defined scope and objectives.
Authorization processes manually documented with basic monitoring in place.
|
|
4 - Comprehensive
|
Dedicated risk management systems in place using automated vulnerability scans and
in-depth security assessments. Key security controls continuously monitored via dashboards
displaying critical alerts and key metrics.
|
|
5 - Advanced
|
Assessment and authorization workflows managed using automated governance, risk, and
compliance solutions. Real-time risk insights continuously provided via AI-driven
monitoring.
|
The CM - Configuration Management NIST SP 800-53 control family covers implementing, managing, and enforcing system
and software configurations for security and compliance.
The following CM - Configuration Management controls are included in the Cyber Risk
Quantification security practices assessment:
-
CM-2 Baseline Configuration
-
CM-3 Configuration Change Control
-
CM-5 Access Restrictions for Change
-
CM-6 Configuration Settings
-
CM-7 Least Functionality
-
CM-8 System Component Inventory
-
CM-10 Software Usage Restrictions
-
CM-11 User-Installed Software
-
CM-12 Information Location
The following table describes implementation levels for the CM - Configuration Management
control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No standardized security configurations in place. No system inventory established,
and configuration changes made without testing or approval.
|
|
2 - Basic
|
Manual system inventory and configuration management plan established with limited
documentation. Configuration settings restricted to authorized users.
|
|
3 - Functional
|
Standardized security configuration baselines established for systems and software.
All changes formally documented, reviewed, and approved before implementation.
|
|
4 - Comprehensive
|
Security configuration baselines enforced using automated tools and templates. Changes
logged and validated before implementation as part of regular security impact analysis.
|
|
5 - Advanced
|
Fully automated security configuration and compliance management integrated into security
operations. Real-time validation of configuration changes and automatic remediation
of unauthorized or non-compliant security configurations.
|
The CP - Contingency Planning NIST SP 800-53 control family covers preparing for and recovering from system interruptions,
security incidents, and disasters.
The following CP - Contingency Planning controls are included in the Cyber Risk Quantification
security practices assessment:
-
CP-2 Contingency Plan
-
CP-6 Alternate Storage Site
-
CP-7 Alternate Processing Site
-
CP-9 System Backup
-
CP-10 System Recovery and Reconstitution
The following table describes implementation levels for the CP - Contingency Planning
control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No documented preparation or recovery plan. Data backups performed manually and irregularly,
with no recovery procedure in place.
|
|
2 - Basic
|
Basic preparation and recovery plans for critical systems established but untested.
|
|
3 - Functional
|
Formal recovery plans documented with defined roles and responsibilities. Backup and
recovery processes tested on a regular schedule.
|
|
4 - Comprehensive
|
Automated backup and recovery processes implemented across the organization. Business
continuity and disaster recovery plans regularly tested against defined recovery time
objectives.
|
|
5 - Advanced
|
Recovery processes continuously validated through automated testing, with AI-driven
monitoring proactively identifying and mitigating business continuity risks.
|
The IA - Identification and Authentication NIST SP 800-53 control family covers authenticating and protecting user, system,
and device identities.
The following IA - Identification and Authentication controls are included in the
Cyber Risk Quantification security practices assessment:
-
IA-2 Identification and Authentication (Organizational Users)
-
IA-3 Device Identification and Authentication
-
IA-4 Identifier Management
-
IA-5 Authenticator Management
-
IA-6 Authentication Feedback
-
IA-7 Cryptographic Module Authentication
-
IA-8 Identification and Authentication (Non-Organizational Users)
-
IA-9 Service Identification and Authentication
-
IA-11 Re-authentication
-
IA-12 Identity Proofing
The following table describes implementation levels for the IA - Identification and
Authentication control family in the Cyber Risk Quantification security practices
assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No authentication policies in place. Weak or default passwords and shared accounts
permitted.
|
|
2 - Basic
|
Basic password policy enforced requiring specified length or complexity. Process for
creating and disabling accounts established and followed.
|
|
3 - Functional
|
Strong password policies including password history and age enforced. Multi-factor
authentication (MFA) required for privileged accounts.
|
|
4 - Comprehensive
|
MFA required for all network, remote, and sensitive data access. Identity management
centralized and automated across the organization.
|
|
5 - Advanced
|
All access verified through zero-trust architecture. AI-driven behavioral analysis
enables real-time account compromise detection and response.
|
The MP - Media Protection NIST SP 800-53 control family covers protecting physical and digital media, including
data, records, and files, during use, storage, and disposal.
The following MP - Media Protection controls are included in the Cyber Risk Quantification
security practices assessment:
-
MP-7 Media Use
The following table describes implementation levels for the MP - Media Protection
control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No formal media management procedures. No policies for handling, storing, or sanitizing
media.
|
|
2 - Basic
|
Sanitization of media before disposal required. Access to media logged and restricted
to authorized users.
|
|
3 - Functional
|
Policies for secure media transfer, storage, and disposal documented and enforced.
Digital media encrypted during storage and transfer.
|
|
4 - Comprehensive
|
Centralized media tracking with user and change logging implemented across the organization.
Removable media such as USB drives generally prohibited, with approved exceptions
tracked.
|
|
5 - Advanced
|
Media lifecycles automated and centrally enforced, with sensitive data automatically
detected and encrypted. Permitted removable media use automatically logged and monitored.
|
The RA - Risk Assessment NIST SP 800-53 control family covers identifying and analyzing risks to organizational
operations, systems, and assets.
The following RA - Risk Assessment controls are included in the Cyber Risk Quantification
security practices assessment:
-
RA-5 Vulnerability Monitoring and Scanning
-
RA-9 Criticality Analysis
-
RA-10 Threat Hunting
The following table describes implementation levels for the RA - Risk Assessment control
family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No risk assessments performed. Security issues addressed only as they arise.
|
|
2 - Basic
|
Manual risk assessments performed as needed, such as during initial system implementation.
Vulnerabilities identified and documented, but not consistently monitored or mitigated.
|
|
3 - Functional
|
Formal risk assessments performed on a regular basis organization-wide. Vulnerabilities
identified through scheduled assessments and prioritized for mitigation.
|
|
4 - Comprehensive
|
Dedicated risk management teams use automated tools to continuously assess the organization
for risk. Threats and vulnerabilities continuously monitored via threat intelligence
feeds and automated vulnerability scanning.
|
|
5 - Advanced
|
AI-driven systems use predictive analytics to proactively identify risks before they
occur. Internal and external threat intelligence used to counter emerging threats.
|
The SA - System and Services Acquisition NIST SP 800-53 control family covers integrating security into system and service
acquisition and development.
The following SA - System and Services Acquisition controls are included in the Cyber
Risk Quantification security practices assessment:
-
SA-3 System Development Life Cycle
-
SA-4 Acquisition Process
-
SA-8 Security and Privacy Engineering Principles
-
SA-9 External System Services
-
SA-10 Developer Configuration Management
-
SA-11 Developer Testing and Evaluation
-
SA-15 Development Process, Standards, and Tools
-
SA-16 Developer-Provided Training
-
SA-17 Developer Security and Privacy Architecture and Design
-
SA-22 Unsupported System Components
The following table describes implementation levels for the SA - System and Services
Acquisition control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
Security not considered during system or service acquisition or development. New systems
deployed without security assessment.
|
|
2 - Basic
|
Basic security requirements included in system and service acquisition processes.
New systems informally reviewed.
|
|
3 - Functional
|
Security requirements formally documented and fully integrated into the system development
lifecycle. Security requirements included in acquisition contracts and tested before
system deployment.
|
|
4 - Comprehensive
|
Detailed supply chain risk management integrated into a standardized, organization-wide
acquisition process. All service providers vetted for security practices before contracts
are signed.
|
|
5 - Advanced
|
Security testing, code scanning, and continuous monitoring automated across all stages
of development and acquisition.
|
The SC - System and Communications Protection NIST SP 800-53 control family covers protecting information systems and communications
from unauthorized access and disclosure.
The following SC - System and Communications Protection controls are included in the
Cyber Risk Quantification security practices assessment:
-
SC-2 Separation of System and User Functionality
-
SC-3 Security Function Isolation
-
SC-4 Information in Shared System Resources
-
SC-6 Resource Availability
-
SC-7 Boundary Protection
-
SC-8 Transmission Confidentiality and Integrity
-
SC-10 Network Disconnect
-
SC-12 Cryptographic Key Establishment and Management
-
SC-13 Cryptographic Protection
-
SC-16 Transmission of Security and Privacy Attributes
-
SC-17 Public Key Infrastructure Certificates
-
SC-18 Mobile Code
-
SC-20 Secure Name/Address Resolution Service (Authoritative Source)
-
SC-21 Secure Name/Address Resolution Service (Recursive or Caching Resolver)
-
SC-22 Architecture and Provisioning for Name/Address Resolution Service
-
SC-23 Session Authenticity
-
SC-26 Decoys
-
SC-28 Protection of Information at Rest
-
SC-29 Heterogeneity
-
SC-30 Concealment and Misdirection
-
SC-31 Covert Channel Analysis
-
SC-34 Non-modifiable Executable Programs
-
SC-35 External Malicious Code Identification
-
SC-36 Distributed Processing and Storage
-
SC-37 Out-of-band Channels
-
SC-38 Operations Security
-
SC-39 Process Isolation
-
SC-41 Port and I/O Device Access
-
SC-43 Usage Restrictions
-
SC-44 Detonation Chambers
-
SC-46 Cross Domain Policy Enforcement
The following table describes implementation levels for the SC - System and Communications
Protection control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No firewalls or other network boundary protections in place. Outbound communications
not encrypted.
|
|
2 - Basic
|
Firewalls in place to provide basic protection between corporate and external networks.
Simple encryption used for some sensitive outbound communication.
|
|
3 - Functional
|
All corporate and external network traffic monitored. All sensitive communication
and stored data encrypted.
|
|
4 - Comprehensive
|
Intrusion prevention system (IPS) monitors network traffic for suspicious or malicious
activity. Perimeter network established using firewalls, proxy servers, and gateways
to separate corporate and external networks.
|
|
5 - Advanced
|
All corporate and external traffic automatically inspected and authenticated using
zero-trust principles. Extensive network segmentation and continuous monitoring enforced.
|
The SI - System and Information Integrity NIST SP 800-53 control family covers securing information systems and protecting
system data integrity.
The following SI - System and Information Integrity controls are included in the Cyber
Risk Quantification security practices assessment:
-
SI-2 Flaw Remediation
-
SI-3 Malicious Code Protection
-
SI-4 System Monitoring
-
SI-5 Security Alerts, Advisories, and Directives
-
SI-7 Software, Firmware, and Information Integrity
-
SI-8 Spam Protection
-
SI-10 Information Input Validation
-
SI-12 Information Management and Retention
-
SI-14 Non-persistence
-
SI-15 Information Output Filtering
-
SI-16 Memory Protection
-
SI-23 Information Fragmentation
The following table describes implementation levels for the SI - System and Information
Integrity control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No antivirus, malware protection, or patch management systems used. Software installed
without approval and changes not monitored.
|
|
2 - Basic
|
Antivirus or malware protection systems installed on individual user devices. Automatic
updates configured, manual patching occasionally performed.
|
|
3 - Functional
|
Centralized antivirus and malware protection used organization-wide. Formal patch
management process established and regularly followed.
|
|
4 - Comprehensive
|
Advanced endpoint protection solutions monitor for suspicious or malicious activity
in real time. System vulnerabilities promptly addressed using automated patch management.
|
|
5 - Advanced
|
AI-driven security solutions detect and automatically respond to existing and zero-day
threats and vulnerabilities. System files continuously scanned for unauthorized changes
using automated integrity monitoring.
|
The SR - Supply Chain Risk Management NIST SP 800-53 control family covers managing and mitigating risks associated with
product and service supply chains.
The following SR - Supply Chain Risk Management controls are included in the Cyber
Risk Quantification security practices assessment:
-
SR-4 Provenance
-
SR-5 Acquisition Strategies, Tools, and Methods
-
SR-6 Supplier Assessments and Reviews
-
SR-11 Component Authenticity
The following table describes implementation levels for the SR - Supply Chain Risk
Management control family in the Cyber Risk Quantification security practices assessment:
|
Level
|
Description
|
|
1 - Incomplete
|
No established process for vetting suppliers or assessing purchased product security.
|
|
2 - Basic
|
Basic security clauses included in vendor contracts. New products informally evaluated
for security.
|
|
3 - Functional
|
Formal supply chain risk management process documented and followed. Due diligence
checks performed for critical vendors.
|
|
4 - Comprehensive
|
Dedicated system continuously evaluates and mitigates supply chain risks. Third-party
products and services monitored and threat intelligence shared across organizations.
|
|
5 - Advanced
|
Supply chain security posture automatically and continuously monitored for real-time
risk insights. Product integrity and supplier security automatically verified.
|
To collect security practice questionnaire responses from people who are not Cyber
Risk Quantification users, see Self-assessment data collection forms.


