The notifier application, available both for Windows and macOS, communicates the state
of the agent and relay to client machines using either the Windows notification area
or macOS Notification Center. The notifier displays pop-up user notifications when
the agent begins a scan, or blocks malware or access to malicious web pages.
The notifier does consume resources (or "has a footprint") on the client machine,
requiring on Windows less than 1MB of disk space and 1MB of memory, and on macOS less
than 10MB of disk space and 50MB of memory. When the notifier is running, the notifier
icon
 appears in the taskbar in the lower right of a Windows screen or
appears in the taskbar in the lower right of a Windows screen or
 in the menu bar at the top of a macOS screen. The notifier is automatically installed
by default with the agent for Windows and macOS computers. Use the page to import the latest version for distribution and upgrades.
in the menu bar at the top of a macOS screen. The notifier is automatically installed
by default with the agent for Windows and macOS computers. Use the page to import the latest version for distribution and upgrades.
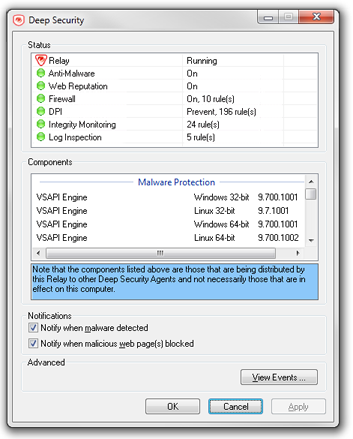
NoteOn computers running a relay-enabled agent (supported on Windows), the notifier displays
the components that are being distributed to agents or appliances, not which components are in effect on the local computer.
|
How the notifier works
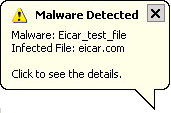
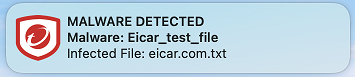
When malware is detected or a malicious site is blocked, the agent sends a message
to the notifier, which displays a pop-up message in the notification area or Notification
Center.
If malware is detected, the notifier displays a pop-up message similar to the following
examples:
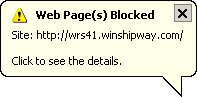
When a malicious web page is blocked, the notifier displays a pop-up message similar
to the following examples:

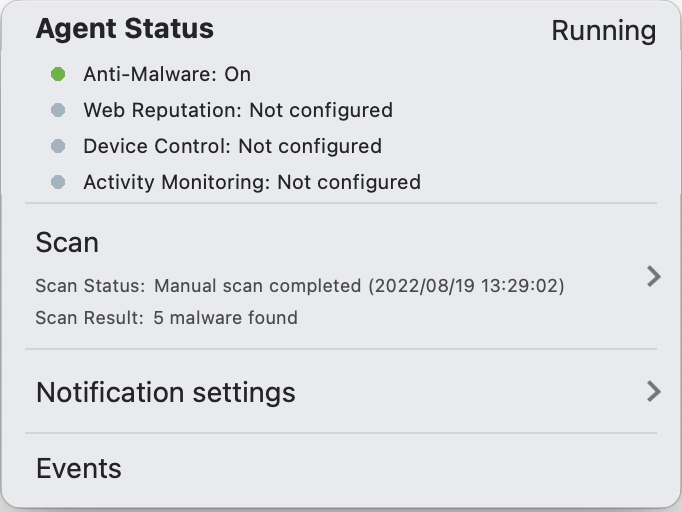
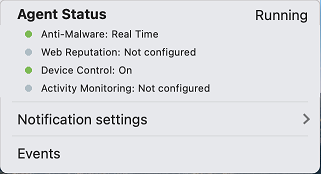
The notifier also provides a console utility for viewing the current protection status
and (for Windows only) component information, including pattern versions. The console
utility allows the user to turn the pop-up notifications on or off and access detailed
event information.
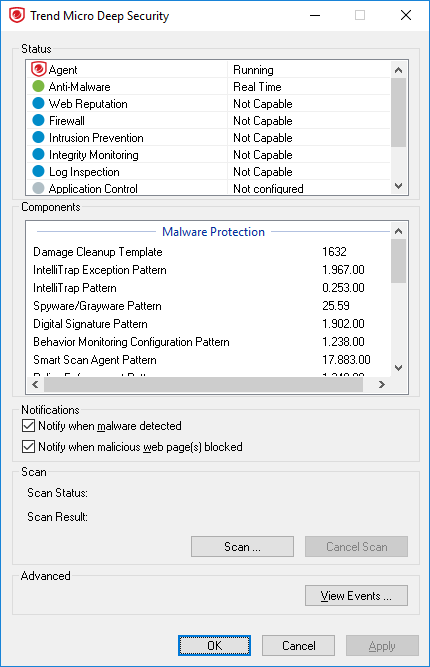
The notifier console on Windows:
The notifier console on macOS:
TipYou can also turn off pop-up notifications for certain computers or for computers
that are
assigned a particular policy by going to the Server & Workload Protection
and settings Suppress all pop-up notifications on
host to Yes. The messages still appear as alerts or
events in the Server & Workload Protection console.
|
When the notifier is running on a computer hosting a relay (where supported), the
notifier's display shows the components being distributed by the relay and not the
components that in effect on the computer.
When the notifier is running on a computer with the scanner feature enabled, it shows
that Scanner is running. A computer running Scanner cannot be a relay.
Trigger a manual scan
If the checkbox is selected that enables an agent to trigger a manual scan in the
notifier application, the notifier console will include a panel titled Scan. The notifier
will use the scan configuration assigned from the computer editor or the policy editor,
in the editor's Anti-Malware tab, in the General horizontal tab, in the Manual Scan section. For more details, see Create or edit a malware scan configuration.
A scan cannot be triggered:
- when the agent is being upgraded
- when there is an ongoing server-side scan already taking place
- if the scan configuration is empty
Windows
Procedure
- To start a manual scan by the agent, in the Scan panel, click Scan.
- Select the folders to scan in the folder tree and click Scan.
- For a Full Scan, select This PC to start a scan of all files
- For a Custom Scan, select one or more files or folders to start a scan.
Next steps
Once the scan is completed, the Scan Result will display the number of detected malware
items. To view details of these items, click View Events in the notifier's Advanced panel.
NoteAn ongoing scan will be halted if it has been triggered on a computer that is not
available. For example, the user logs out of the computer after the scan has been
started.
|
macOS
From the notifier console, select the Scan menu item, then from the sub-menu, do one of the following:
- Click Full Scan to start a scan of all files
- Click Custom Scan to select one or more files or folders to scan, then start a scan.
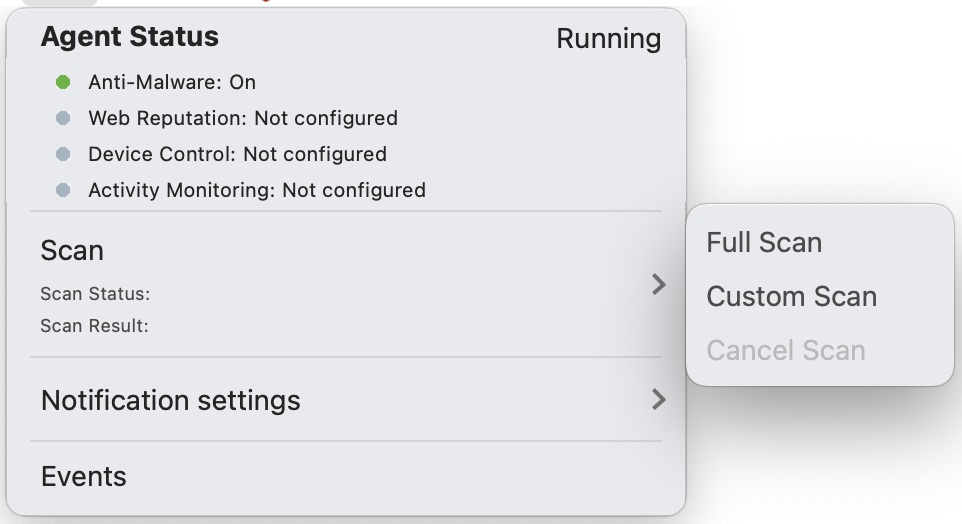
To cancel a manual scan is already in progress, select the Scan menu item, then from the sub-menu, click Cancel Scan.
NoteThe server can also cancel a manual scan in progress.
|
When an ongoing scan was triggered from the notifier console:
- the scan will continue if the user has logged out
- the scan will be terminated if the computer has been restarted
Once a scan has completed, the notifier console will display in its Scan panel the
number of malware items found. To view details for each malware item, select the Events menu item. This detailed information is also available from the computer editor or
the policy editor in the editor's Anti-Malware tab, in the Anti-Malware Events horizontal tab.