The Connected Threat Defense strategy integrates many TrendAI™ products. The
following diagrams illustrate how the major products interact.
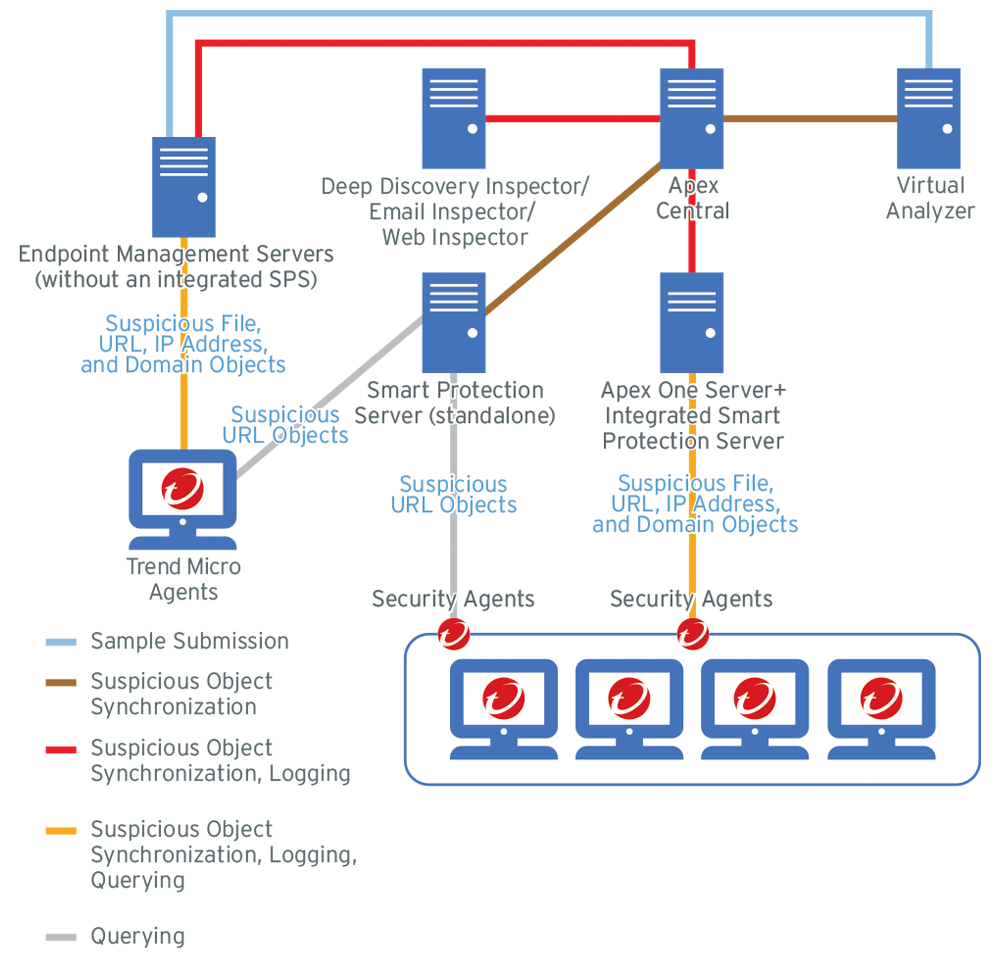
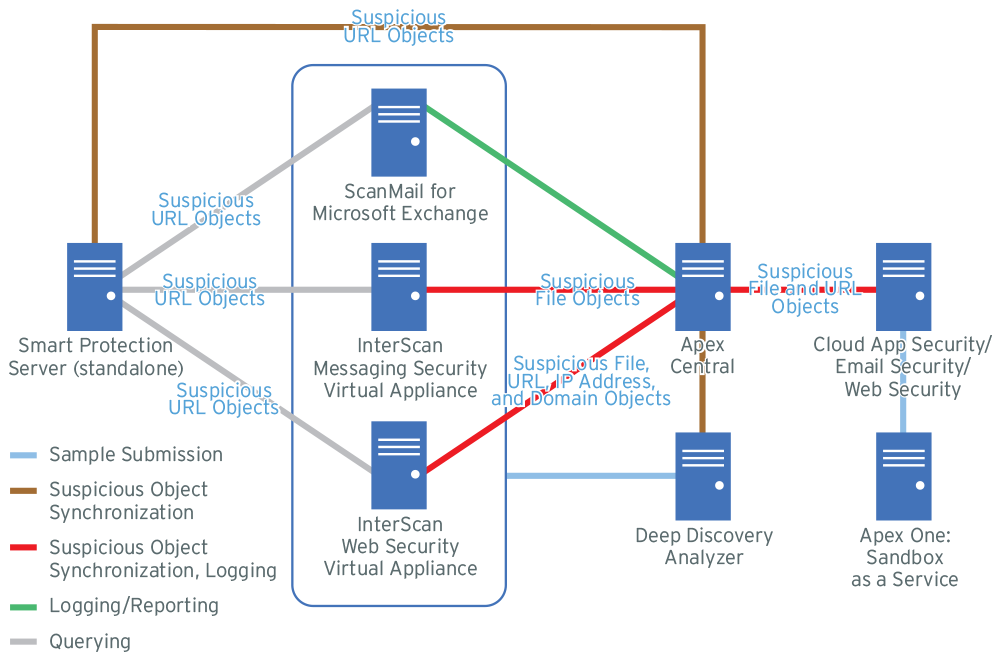
TrendAI™ Apex Central further
monitors other registered TrendAI™ products through log analysis and comparison of detected
files with the synchronized suspicious object lists.
For TrendAI™ Apex Central
registration and suspicious object list synchronization information for each major
product, refer
to the following:


