|
|
|
|
Feature
|
Description
|
|---|---|
|
Advanced anti-malware protection
|
The Advanced Threat Scan Engine (ATSE) uses a combination of pattern-based scanning
and aggressive heuristic scanning to detect document exploits and other threats used
in targeted attacks.
For more information about ATSE, see About Advanced Threat Scan Engine.
|
|
Integration with Deep Discovery Advisor
|
Trend
Micro™ Deep Discovery
Advisor is a separately licensed product that provides unique security visibility
based on Trend Micro’s proprietary threat analysis and
recommendation engines. Deep Edge integrates
with the Virtual Analyzer in Deep Discovery Advisor.
For more information about Deep Discovery Advisor, see About Deep Discovery Advisor.
|
|
Streamlined network configuration
|
To simplify network configurations, Deep Edge
streamlines the settings for interfaces, DNS, DHCP and DNS forwarding, and bridged
interfaces.
|
|
Feature
|
Description
|
|---|---|
|
Dual ISP and WAN support
|
Deep Edge can now support dual WAN or ISP
connections.
|
|
Enhanced IPS performance
|
Deep Edge Intrusion Prevention Systems (IPS)
performs deep content inspection on all traffic to stop harmful activities. Deep Edge 2.5 now has the capabilities to scan
traffic with over 7000 easily-configured predefined IPS rules by setting filtering
criteria about the severity level, affected operating systems, release date, or
traffic categories. For details, see IPS Security.
|
|
Granular application control
|
Application control objects now include specific behaviors within the application,
such as only limiting video calls or uploading files, to set granular policy
rules.
|
|
New custom URL category objects
|
Deep Edge 2.5 supports customized URL category
objects. For details, see Adding a Custom URL Category.
|
|
Command & Control (C&C) Contact Alert Services
|
Command & Control (C&C) Contact Alert Services provides Deep Edge with enhanced detection capabilities to
mitigate the damage caused by advanced persistent threats and targeted attacks by
blocking traffic from high-risk sources.
A new C&C Callback Attempts widget tracks advanced
persistent threat activity in your network by providing actionable intelligence
about the user, the compromised host, and how Deep Edge enforced policy actions. For details,
see C&C Contact Alert Widget.
|
|
Improved widget framework
|
Several improvements to the widget framework have increased performance,
reliability and speed of the dashboard widgets.
|
|
Increased configuration visibility
|
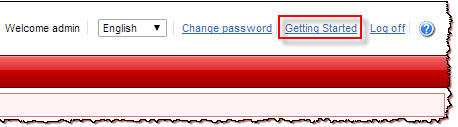
A new Getting Started guide is available to simplify the setup
process. Click Getting Started directly from the web console
to view the help content.
 |
|
Improved NAT rules
|
Each Deep Edge 2.5 NAT rule now has a description
parameter to easily differentiate between multiple SNAT and DNAT configurations.
|
|
More robust log analysis
|
Deep Edge 2.5 enhances log presentation in the
dashboard, log query results, and reports.
|
|
Feature
|
Description
|
|---|---|
|
Bandwidth Control
|
Peer-to-peer downloading, video streaming and instant message applications consume
network bandwidth and can impact productivity. Deep Edge 2.1 supports using bandwidth
control to reduce network congestion by controlling communications, reducing
unwanted traffic and allowing critical traffic or services the appropriate bandwidth
allocation. For details, see About Bandwidth Control.
In addition to policy settings, a new Bandwidth Control widget illustrates affected
traffic. For details, see Bandwidth Control Widget.
|
|
VPN enhancements
|
Deep Edge 2.1 enhances VPN
compatibility:
For details, see Virtual Private Network.
|
|
Mobile VPN compatibility
|
Deep Edge 2.1 Mobile VPN supports
multiple local domains. For details, see Configuring Advanced Mobile VPN Settings.
|
|
Local users and groups
|
Local user and group management allows for authentication when an organization does
not use Active Directory or LDAP authentication. Additional Deep Edge 2.1 enhancements include:
For details, see Local User and Group Management.
|
|
Feature
|
Description
|
|---|---|
|
HTTPS Inspection
|
The HTTPS Inspection feature in Deep Edge
allows you to enable or disable HTTPS inspections, configure client certificate
requests, and exclude specific websites, URLs, and IP addresses from inspection. For
more information, see About HTTPS Inspection.
|
|
Mobile VPN Support
|
Deep Edge, a gateway device,
provides VPN services not only to laptops or desktops but also mobile devices.
Mobile VPN offers support for mobile devices in the “closed” environment of Apple
iOS or the “open source“ environment of Android. For more information, see Mobile VPN.
|
|
Anti-DoS Capability (and Report)
|
Deep Edge prevents Denial of
Service (DoS) or a Distributed Denial of Service (DDoS) attacks, which attempt to
make a machine or network resource unavailable to users, and is intended to
temporarily or indefinitely interrupt or suspend services to a host connected to the
Internet.
Typical attacks involve saturating the target machine with external communication
requests, such that the machine can no longer respond to legitimate traffic or
responds so slowly it is rendered unavailable. Such attacks usually lead to server
overload. For more information, see About Anti-DoS.
|
|
End-user Notifications
|
Deep Edge provides end-user notifications for violations of the following policies: Web Reputation Services (WRS), URL Filtering, anti-malware, blacklisted URLs, file extensions detections, IPS and certificate failure (server and client). For more information, see About User Notifications. |
|
Email Security Solution
|
Deep Edge processes SMTP or POP3
email messages, scans them, and either cleans infected email messages and delivers
them or performs the user-selected action set in the policy on email messages in
violation. Email messages can be quarantined and delivered later. For more
information, see Anti-Spam Profiles.
|
|
SSL VPN Enhancements
|
Deep Edge supports Secure Sockets
Layer Virtual Private Network (SSL VPN), a form of VPN that can be used with a
standard Web browser. The Deep Edge SSL VPN solution requires the installation of client
software, and is ideal for applications including web-based email, business and
government directories, file sharing, remote backup, remote system management, and
consumer-level electronic commerce. For more information, see Secure Socket Layer Virtual Private Network.
|